
Silvano Rebai - Fotolia
SIP protocol primer: Learn the SIP basics
With the rise of IP communications, SIP has become the standard for initiating communication across a network. Learn the basics of SIP, including how it works and why you need it.
The Session Initiation Protocol is a necessary piece of the communications puzzle. With the explosion of the number of communication devices, people are more connected than ever before. IP-enabled devices are increasingly common for communication with one another and SIP is how most people manage communications between IP-enabled devices.
The protocol was developed by the Internet Engineering Task Force and is modeled after the Hypertext Transfer Protocol. SIP is the standard for communication interoperability between any mix of IP devices.
"SIP serves as the foundation of just about everything that enables our business communications today," said Michael Brandenburg, an analyst at Frost & Sullivan. "The phone on a user's desk, the video conferencing room and even carrier dial tone into an organization rely on the SIP protocol to make those connections."
What is SIP and how does it work?
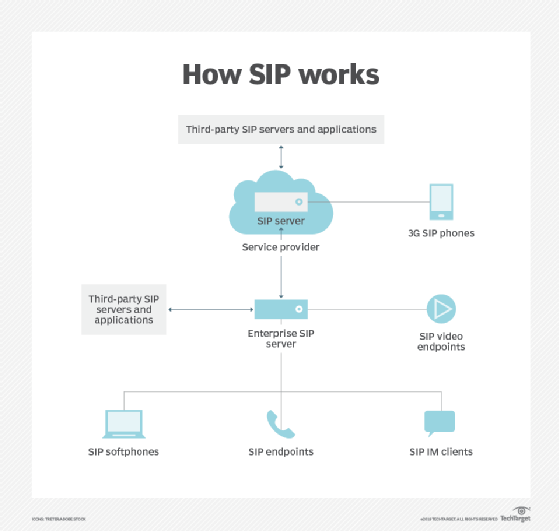
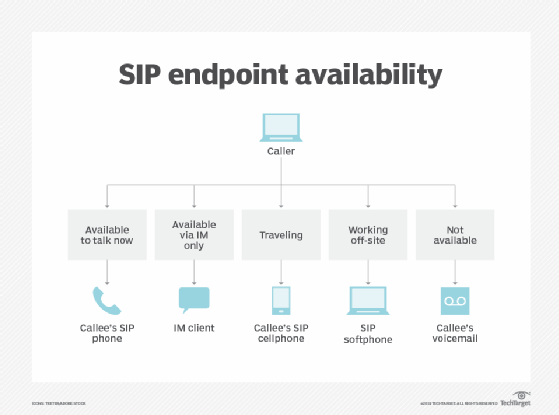
SIP is used to start IP-based communication sessions between two network endpoints, such as a VoIP call, video chat or some other form of messaging. SIP determines attributes such as user location and availability, the user's communications capabilities, and what the setup and management of a session will be.
While SIP is essential to initiate and end communication sessions, the actual delivery of sessions is handled by codecs. SIP should be viewed as an application layered on top of communications. Developers can customize SIP to handle more than just phone calls by writing custom applications that can accommodate a whole host of communication modes.
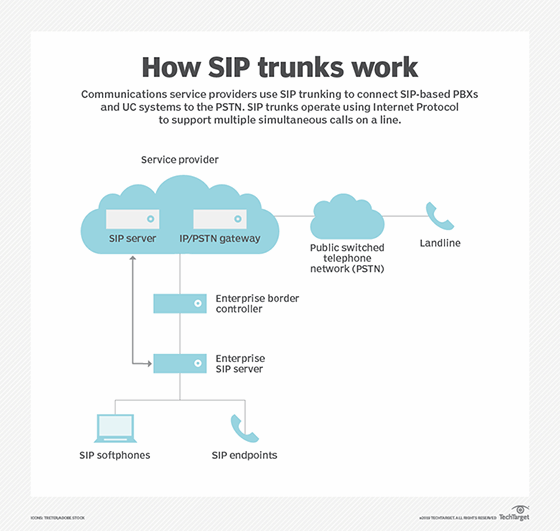
A service closely tied to SIP is SIP trunking, which allows for connections between VoIP phone systems and traditional landline PBXs. SIP trunking works when a VoIP phone system connects to a SIP provider network using a broadband internet connection. This allows the SIP provider to connect calls from IP endpoints to traditional phone endpoints.
Why should you know about SIP basics?
As IP-based communication grows in popularity, the ability to establish connections between devices, such as a VoIP phone and a mobile device, is essential. SIP was created to be a standard protocol to facilitate IP communication.
Without SIP, communication between different devices would require additional transcoding, as devices often use different codecs to support sessions. In these cases, a provider might rely on a proprietary protocol for transcoding, which requires additional steps and devices to ensure the transcoding is done correctly and the session connects the way it should.
SIP ensures that disparate devices can establish a connection by transcoding directly within the protocol, which helps conserve bandwidth. Moreover, many businesses will need to know if their SIP provider offers SIP trunking to ensure the ability to successfully make calls outside of the business.
What should you know about SIP?
The most important aspect of setting up SIP is to know your organization's network. Assuming the network can handle SIP traffic could bring your communications to a screeching halt. Most providers use a bandwidth calculator to understand your requirements.
In addition to basic SIP testing tools, most SIP service providers offer some kind of trial period. It's prudent to test sample calls both internally and externally to get a clearer idea of how your network and SIP provider will handle traffic.
Problems with SIP trunks can have a major impact on your business, as calls to PBXs will be unable to connect. However, end-user organizations and SIP providers often disagree on where SIP trunking problems lie.
According to the SIP School's "The SIP and Cloud survey 2018," the majority of vendors attribute SIP issues to problems with the end-user PBX configuration. However, the majority of customers ascribe SIP issues to their service provider. Open communication is necessary between SIP providers and end-user organizations when it comes to service quality and expectations.
When thinking about SIP basics, you should also consider adding Session Border Controllers (SBCs). An SBC can act as a firewall for your network, providing greater security for your communications. The SIP School Survey revealed, however, that 15% of end-user organizations had no basic SBC installed. Most PBX vendors and SIP providers, like Avaya and Cisco, offer some kind of SBC, but organizations can also buy SBC services from router vendors or independent resellers.
The SIP School recommends that you take advantage of the trial period offered by most SIP vendors, as a provider will often work with you to tailor the service to your business needs. Providers also have tools for measuring the quality of their SIP service. When making SIP purchasing decisions, check what SIP monitoring tools your vendor can provide.








