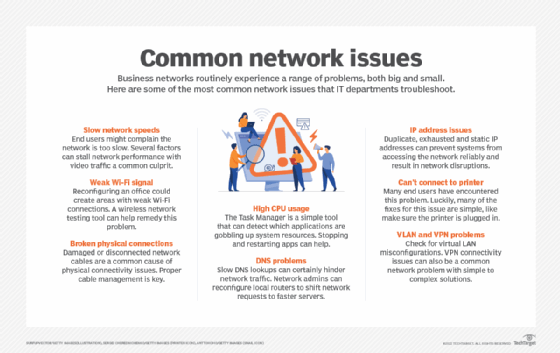
9 most common network issues and how to solve them
Slow network speeds, weak Wi-Fi signals and damaged cabling are just some of the most common network connection issues that IT departments need to troubleshoot.
Business networks are complex, and many things can go wrong that disrupt network performance. End users often complain about what appears to be poor application performance, and there can be many possible reasons for these hiccups. Here are nine of the most common network issues to troubleshoot.
1. Slow network
Users complain the network is too slow. There can be many reasons why a network that provided adequate performance in the past is now frustrating its users. For instance, a new application, such as video conferencing or online training videos, may have been added. A failing switch port or link could cause traffic to route around the failure and overload another link.
In other cases, the network could be part of a larger organizational network. As a result, a change in the larger network has resulted in more traffic through the internet connection point, slowing responses to cloud-resident applications.
Another network speed issue could emerge if employees decide to download high-definition videos while at work because downloading in the office is faster than using their home internet connection. A network monitoring tool helps solve any of these common network issues.
2. Weak Wi-Fi signal
Wi-Fi signal strength may be adequate almost everywhere, but it could be weak or nonexistent in other areas. Rearranging an office area can result in a weak wireless connection, where signal strength had been adequate before the move. For example, a large metal object, like a file cabinet, can block the Wi-Fi signal.
Devices such as microwave ovens, cordless phones and Bluetooth can interfere with Wi-Fi signals, too. A Wi-Fi network test tool can help identify the source of the problem.
3. Physical connectivity issues
A network connection can suddenly break because of physical connectivity issues. A common problem is when a network cable becomes damaged or knocked loose. Cables might be added or removed from a switch, and one of the other cables might accidentally get disconnected.
Or a cable was damaged when it was pulled around a sharp edge while work was done on the heating or air conditioning pipes. It should be clear from the segment of the network affected which cable was damaged. But finding the problem along a cable stretching across the ceiling may be time-consuming.
4. Excessive CPU usage
Task Manager is the first thing to use to find which application is using a high proportion of system resources, such as CPU, memory or disk space. This basic troubleshooting step may not reveal a problem since some applications may be performing complex calculations, receiving high-speed video or interacting with large databases. A virus may also consume resources, so make sure antivirus software is up to date.
If an application has been running for a long time, it may slowly leak resources. The quickest way to improve performance is to stop and restart the application, although sometimes you may need to stop and restart the entire system. Updating device drivers may also improve performance.
Task Manager also shows applications you didn't know were running in the background. One example would be Windows including games upon system startup. Editing startup files can eliminate this problem.
5. Slow DNS lookups
The DNS matches the common name used to match server or service names with the internet address that routes a network request. For commonly used names, the matchup is probably already stored in the system's DNS cache, and the lookup is quick. For less commonly used names, the matchup may be stored in a more distant cache, such as the root server of the top-level name, such as .com, .org or a national root, such as .uk.
Each DNS server along the path checks its cache before making a request to the next server along the path. The next server then checks its cache, repeating the process. If lookup is slow, there may be a slow link along the path or a slow or overloaded server. To address this issue, your local network administrator can reconfigure local routers to shift requests to a faster chain of servers.
6. Duplicate and static IP addresses
On a network, no two systems can share the same internet address. If there are duplicate internet addresses, neither system can access the network reliably. The addresses for most network devices are assigned when Dynamic Host Configuration Protocol (DHCP) boots up the systems on the local network. DHCP maintains a pool of addresses assigned to the local network, assigning a different address from the pool to each system.
Workstations are not assigned permanent addresses but receive one for a limited time from DHCP. Systems re-request before the time runs out and usually receive the same address. If the system shuts down without re-requesting and the time runs out, it loses this address and may receive a different one upon startup.
The DHCP administrator may assign a static IP address to some network devices, such as printers or web servers, because external systems won't be updated if an address changes. One issue is users sometimes set up a private web server to support a hobby, allocating a static address without informing the network administrator. Both share a DHCP server in either an organization or home network. So, if the static address matches one assigned by DHCP, it disrupts the network.
Often, these private web servers are set up to upload and download licensed music or video and consume excessive network bandwidth.
7. Exhausted IP addresses
Internet addresses are in limited supply. Each service provider is given a supply based on the expected number necessary. Most familiar are the IPv4 addresses, which were originally thought to be adequate so every system could be allocated one. But, with the proliferation of cellphones and other devices, it's been necessary to move to IPv6 with 128-bit addresses for some networks.
A widely used method to stretch the supply of addresses is Network Address Translation (NAT), a feature often built into routers. Each is assigned a single internet address allocated from the worldwide set of addresses. Its internal DHCP server allocates private addresses to systems on connected local networks -- usually, an Ethernet or wireless network.
Private addresses generally start with either 10 or 192.168 on networks using 32-bit IPv4 addresses. These address ranges can be used many times, which helps to save addresses. The NAT server maps traffic to its global address to communicate with the internet. Responses are mapped back via the private addresses.
8. Can't connect to printer
When users can't connect to a printer, the first step is to check simple things like whether the printer is plugged in, turned on and has paper. Also, make sure the printer appears on Devices and Printers on Windows. If it does, click to check whether the file is queued.
Sometimes, you need to stop and restart the print spooler, the software that stores files until the printer is ready to print them. Also, check the printer vendor's website because some brands have a downloadable app that can diagnose and fix problems.
If the OS was just upgraded, scan for other people with similar problems, or check Microsoft.com to see if the company is aware of a problem. Shut off the printer, and turn it back on. Also, shut down your system, and turn it back on.
Finally, update printer drivers and your OS. In some cases, you may need to temporarily shut down your antivirus software. For a wireless printer, make sure it's connected to the signal.
9. VLAN and VPN problems
Check for virtual LAN (VLAN) misconfiguration issues. Review the configuration on each switch, carefully comparing configurations to ensure compatibility of switch configuration.
The most common VPN problem is a failure to connect. First, check to see if you're successfully logging in to the service, and make sure your account is up to date and you're entering your correct credentials. Next, check firewall settings. You need to open some ports. Check if that is the problem by temporarily shutting down your firewall. Finally, restart your system.
Try accessing the VPN from a different network, such as switching from Wi-Fi to Ethernet to the router. If there is still a problem, refer to the firewall documentation for other solutions, or contact the VPN vendor support.
In sum, networks are complex, and problems do occur. These are just some of the most common types of network problems. When other types of network issues occur, scan the web for help, or contact network service providers or device vendor support.






