Public vs. private vs. hybrid cloud: Key differences defined
As cloud services and practices mature, it's time to rethink long-held assumptions about the private and public cloud models and consider a hybrid cloud.
Conventional wisdom holds that private clouds are better for workloads that have high compliance or security needs. Public clouds, meanwhile, are ideal for almost anything else. And hybrid cloud is supposed to provide a happy medium by letting businesses use public cloud services on private infrastructure.
However, that logic no longer applies quite so neatly. Public, private and hybrid cloud architectural strategies and platforms have expanded in recent years, and the use cases for each model aren't as clearly delineated as they once were. To decide whether public cloud, private cloud or hybrid cloud -- or a combination of multiple models -- is best for a given workload, consider the following factors and nuances.
What is public cloud?
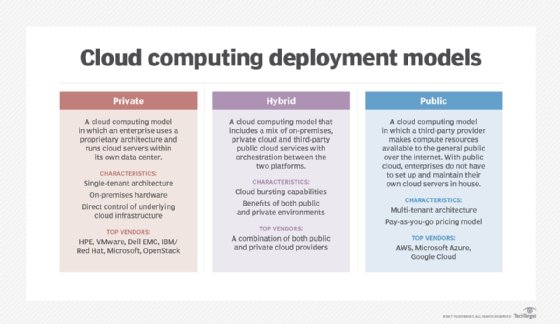
A public cloud provider makes storage, VMs and other services available over the internet to anyone who wants them. Although workloads are isolated at the software level, they run on shared infrastructure.
The main advantages of public cloud include the following:
- Ease of use. Because there is no physical infrastructure to set up and manage, it's simple and fast to start using public cloud services.
- Unlimited scalability. Public clouds provide access to virtually unlimited infrastructure capacity. No matter how many applications you need to run or how much data you want to store, the public cloud can handle it.
- Predictable operating expenses. Most public cloud services are billed on a pay-as-you-go basis, which means businesses can use a fixed operating expense model. They don't have to make capital investments to purchase hosting infrastructure.
What is private cloud?
A private cloud, by comparison, offers cloud-based services only to select users -- typically, those within a certain organization. Traditionally, private clouds run on infrastructure owned by that organization, although services such as Amazon Virtual Private Cloud now let customers build private clouds using public cloud data centers and services. This is one example of how the line separating different cloud architectures has blurred.
There are chief advantages to using private clouds rather than public clouds:
- Control. Because private cloud users typically own both their hosting infrastructure and the software used to run private cloud services, they have total visibility into their cloud and control over how it's configured.
- Security. Private clouds are more secure in some respects because they don't require businesses to share infrastructure with other users. In addition, private clouds can be isolated from the internet if desired to reduce the risk of network-borne attacks. Some public cloud services can also be hidden behind cloud firewalls, but ultimately, it's impossible to disconnect public clouds from the Internet entirely.
- Cost. The total cost of ownership of a private cloud can be lower, especially if businesses keep the private cloud in operation for many years, enabling high ROI on their investment in private cloud hosting infrastructure.
What is hybrid cloud?
Hybrid cloud is a cloud architecture that combines public and private cloud resources.
There are several ways to build a hybrid cloud:
- Running public cloud services on privately owned infrastructure via a platform such as AWS Outposts or Azure Stack;
- Running a platform such as Kubernetes on top of public cloud infrastructure to gain more control and flexibility than businesses would have when using public cloud infrastructure or services directly; or
- Running some workloads in a private cloud or on-prem while others run in a public cloud, with integration or centralized management tooling to administer them.
Of these hybrid cloud models, the first is the most common and is usually what practitioners have in mind when they talk about hybrid cloud today. However, given the multiple ways public and private resources can be combined to create a hybrid cloud, as well as varying historical approaches to building hybrid cloud offerings, there is some ambiguity and debate about what hybrid cloud means or how to build a hybrid cloud.
No matter which approach businesses take, the main goals of a hybrid cloud are to achieve the following benefits simultaneously:
- Control. Hybrid clouds aim to give organizations more control over cloud environments than they'd have in a traditional public cloud.
- Simplicity. By using public cloud resources where they are most useful, hybrid clouds can provide a simpler setup and administration experience than a private cloud or on-premises workloads.
- Security: Hybrid clouds can abate some cloud security challenges by providing more control over where workloads are hosted, how they are secured and which data is available for security monitoring purposes.
Key differences between public, private and hybrid cloud
In general, public, private and hybrid clouds are all capable of providing access to the same types of cloud services. For example, you can run hosted VM instances, object storage services and serverless functions as a service on any type of cloud.
The crucial differences between the cloud models lie in the following:
- Who owns the host infrastructure? In a public cloud model, a public cloud vendor owns and manages the underlying infrastructure. Businesses run their own infrastructure in most private and hybrid clouds.
- Who configures the cloud services? In public clouds, vendors set up cloud services -- such as those that make VM instances or object storage available on demand. This is also the case for hybrid clouds, but not always. On a private cloud, users must configure their own cloud services, although they can use platforms such as OpenStack and Kubernetes to help.
Six factors to consider when choosing public, private or hybrid cloud
Although the differences might seem relatively minor, they evoke several important considerations that affect whether a workload is a good candidate for public, private or hybrid cloud.
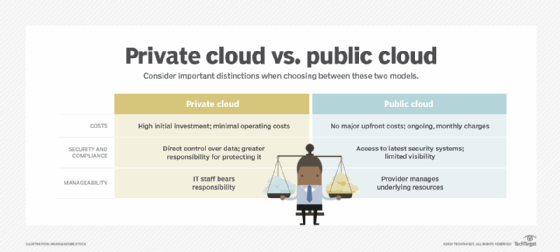
1. Expense model
Public cloud services are typically priced on a pay-as-you-go model. They therefore require no major upfront investment or capital expense. But an organization must carefully monitor cloud spending to avoid racking up big monthly charges.
In contrast, private and hybrid clouds typically require private hosting infrastructure, meaning an organization makes a large upfront investment. The tradeoff for the higher capital expense associated with private and hybrid cloud is a lower ongoing operating expense.
2. Range of cloud services
Most of the core services consumed by public cloud users, such as data storage, VMs and serverless functions, are available in private and hybrid clouds as well. Modern public clouds, however, also provide certain niche services that don't yet have established, prebuilt equivalents on private cloud platforms.
Without services from a public cloud provider, for example, it would be much more difficult to attempt machine learning or IoT initiatives. It might be possible to implement these cloud services, but doing so would require more setup effort and ongoing maintenance than in a public cloud, where the services are preconfigured and available on demand.
3. Compliance and security
In the early days of cloud adoption, many organizations believed that only private clouds could meet strict compliance and security requirements because they provide more control over services and the cloud infrastructure that hosts them. In most cases, that's no longer true. Public clouds now offer sophisticated methods to isolate workloads within specific geographic regions and manage sensitive data.
In addition, most modern compliance frameworks, including the European Union's GDPR and the California Consumer Privacy Act, were written with the cloud in mind. It's entirely possible to remain compliant with these rules while running workloads in the cloud. That said, when you evaluate public cloud versus private cloud, understand that private clouds still offer more fine-grained control over how cloud workloads are configured and hosted.
This can make it easier to meet tight compliance or information security needs. For example, you could configure a private cloud in such a way that data never leaves a local data center, thereby avoiding compliance requirements that apply only when data moves off site. Hybrid clouds also usually offer more control over security and compliance, although this depends on exactly how you build your hybrid cloud.
4. Performance
Because public clouds rely on the public internet to deliver services, their weakest performance link is the limitation on internet bandwidth and connectivity. Workloads that require extensive data transfers might be slower when they run in a public cloud. You can expect high performance and high reliability from private and hybrid clouds in which computing resources are hosted and consumed in the same local site.
This isn't the case, though, in hybrid clouds where public cloud services must integrate with privately hosted infrastructure. They can rely on local networks, which are generally faster than public internet connections. Whichever path you choose, you must ready your network for a cloud environment.
5. Manageability
Users must devote significant effort to set up and manage workloads whether the workloads run in public or private clouds. A public cloud, however, entails less management effort because the service provider not only delivers the computing resources but also manages the hardware for you, such as an infrastructure-as-a-service model.
With a private or hybrid cloud that relies on infrastructure in your own data center, the burden to maintain that hardware is yours.
6. Control and lock-in
Public, private and hybrid clouds all pose lock-in risks in different ways. In a public cloud, it can be difficult to migrate from one cloud platform to another, such as AWS to Azure, because the tooling and configurations for workloads are different.
In a private cloud built using a platform like OpenStack or Kubernetes, you can migrate to different infrastructure easily enough, but only if you keep using the same hosting platform after the migration. This also means you can move a private cloud environment into a public cloud environment relatively easily if you lift-and-shift your OpenStack or Kubernetes environment into public cloud infrastructure.
With hybrid cloud, you might be locked into a specific vendor framework, such as AWS Outposts, although you'll have more flexibility if you build your hybrid cloud using open source software such as OpenStack or Kubernetes.
Public, private, hybrid or combination?
When considering your public cloud and private cloud options, remember that one isn't universally better than the other. But they are different. Private cloud computing generally offers greater control and lower ongoing costs than public cloud, although it requires higher capital expenses and might not offer the variety of services that made public cloud increasingly popular.
Hybrid cloud is an increasingly popular alternative, especially now that platforms such as Azure Stack, Google Anthos and AWS Outposts have matured and made it fairly easy to deploy public cloud services on your own infrastructure. This approach might be particularly compelling for organizations that want the best of both worlds. However, keep in mind that hybrid cloud exposes businesses to some of the drawbacks of public cloud -- such as possibly being locked into a vendor-specific cloud platform, unless you choose an open source hybrid cloud platform -- as well as those of private cloud, such as the cost and management burden of running your own hosting infrastructure.
Keep in mind that there's no reason why you can't use multiple cloud architectures at once. It's possible to run some workloads in a public cloud -- or even in multiple public clouds -- while hosting others in a private or hybrid cloud. This approach will increase management effort because it leaves you with more clouds to administer. But it also gives you more flexibility than you'd get from choosing a public, private or hybrid cloud alone.








