James Steidl - Fotolia
Find network security vulnerabilities by assessing risk
IT staff needs to regularly review network security vulnerabilities and security gaps to battle rising cybersecurity breaches and keep costs under control through risk assessments.
With cybercriminals adding more sophisticated tools and techniques to their arsenals, data breaches are increasing year over year. And the trend looks likely to continue.
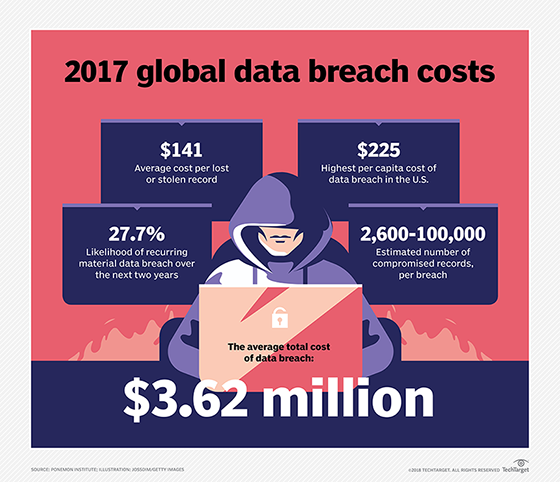
As the number of records breached soars, so do the costs of dealing with them. The numbers are staggering: There were 2.6 billion records globally breached in 2017, marking an 88% jump in data compromises from the year before. According to a 2017 Ponemon Institute study sponsored by IBM, the average data breach costs businesses $3.62 million. While the cost decreased from $4 million per data breach in 2016, companies are having larger breaches.
This intensifies pressure on IT organizations to improve enterprise network security efforts, which should start with a plan to identify network security vulnerabilities and eliminate these holes in its defense. The nature of these security gaps can range from architectural and resource-related to technological.
In order to isolate and correct these issues, the organization needs to conduct a thorough risk assessment. As defined by the National Institute of Standards and Technology, this type of assessment seeks to identify "the cybersecurity risk to organizational operations (including mission, functions, image or reputation), organization assets and individuals."
Through a risk assessment, the enterprise defines the most perilous internal and external threats to its business and outlines what controls and protections are in place. A risk assessment also requires a thorough asset inventory -- systems, network infrastructure technology and nontechnology assets -- including what business services those resources support and which stakeholders are charged with maintaining them.
Too many organizations tie risk and vulnerability assessments to annual compliance testing, rather than understanding these evaluations can reveal critical information to correct flaws before a breach occurs. For risk assessments to be a truly effective element in IT security practices, organizations need to treat these as ongoing efforts, updating asset information and revisiting new IT infrastructure and network security vulnerabilities. Frequent penetration testing is one way to stay on top of possible flaws that could expose the organization to risk.
Compensating for the security skills deficit
For too many organizations, the chief security shortfall is limited security expertise. Whether the business doesn't have enough staff, is limited in skill set depth or a combination of both, the IT organization can find itself scrambling to keep up with an aggressive threat environment. Often deluged with alerts, too many security professionals find themselves tuning out alarms and overlooking threats. Even well-resourced enterprises often struggle to attract cybersecurity talent in a sector that researchers project will have more than 2 million open positions in 2022.
Organizations can and do supplement staff with technology, but they also need to reassess practices. Enterprises should consider the following questions:
- How easy is it to communicate changes in the network threat environment?
- Does the organization have the right tools in place to find and fix new network security vulnerabilities?
- Can network security professionals prioritize responses based on the value of the asset and the criticality of the affected data?
- And does the IT organization have an incident response plan in place to mitigate a breach when one occurs?
Having a system in place that can assign value to an asset -- and adapt that valuation as it changes -- can be helpful in prioritizing remediation activities. Some organizations opt to create their own internal risk valuation tools, or the business can choose a third-party service to help streamline this part of the risk management process.
Tools to identify network security vulnerabilities
Equally important to having the tools to prioritize responses is using these products on a consistent, ongoing basis. Unfortunately, some of the most potentially useful cybersecurity tools are underutilized or not applied appropriately.
One notable gap in organizational security defenses is in how patch management systems are used. An effective patch management program requires a system that applies patches when necessary and fast. If a system is set up to not roll out updates automatically, then the onus is on the network or security administrators to stay on top of zero-day threats. This may mean patches get missed and network security vulnerabilities can be exploited.
Identity and access management is another element that is sometimes not as effective as it should be. Cyberattackers can outmaneuver passwords and other traditional controls. Multifactor authentication can be a crucial tool in defending assets from attack. Setting up multiauthentication access controls on all systems and applications that support it, including remote access gateways and cloud platforms, can deliver an immediate improvement in an organization's security posture.
But perhaps the enterprises best mechanism to improve its defenses is developing, communicating and executing on an effective set of policies to avoid network security vulnerabilities. End-user education is an important part of this equation. Having clear documentation, end-user training and the ongoing communication with staff and users can limit manual errors and improve overall awareness.