service set identifier (SSID)
What is a service set identifier (SSID)?
A service set identifier (SSID) is a sequence of characters that uniquely names a Wi-Fi network. An SSID is sometimes referred to as a network name. This name allows stations to connect to the desired network when multiple independent networks operate in the same physical area.
SSIDs are used in home and business Wi-Fi networks, and are most commonly seen when connecting mobile devices like laptops or smartphones to a wireless network.
SSIDs can reach up to 32 characters in length. Wireless routers and access points broadcast SSIDs so intended users can find and connect to a wireless network. Router manufacturers may create default SSIDs by using the manufacturer's name and adding random numbers and letters. To cause less confusion in an area with multiple wireless networks, changing the default SSID to another string of characters is also common practice.
Some networks may require a password before connecting, while other wireless networks may first require the user to read and agree to an online terms of service before connecting.
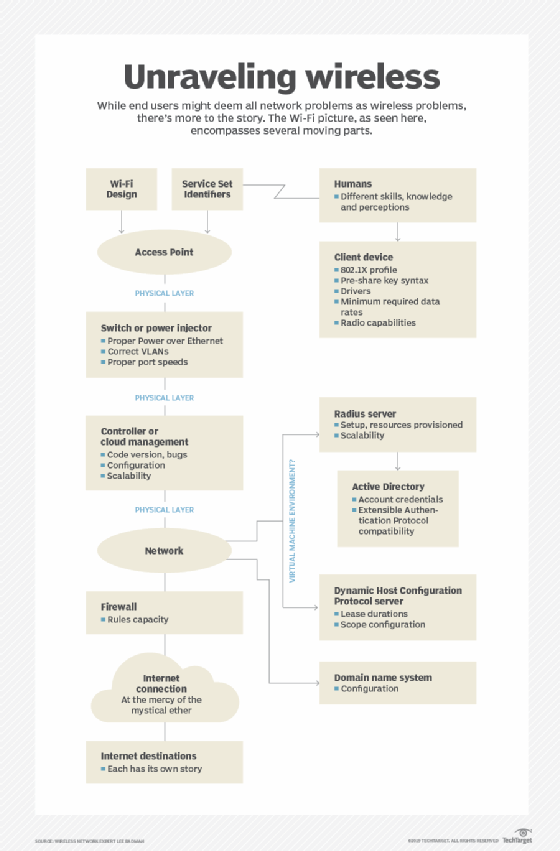
Each set of wireless devices communicating directly with each other is called a basic service set (BSS). Several BSSes can be joined together to form one logical wireless local area network (WLAN) segment, referred to as an extended service set (ESS). An SSID is the 1-32 byte name given to each ESS. Each access point advertises its presence several times per second by broadcasting beacon frames that carry the ESS name.
The Institute of Electrical and Electronics Engineers (IEEE) 802.11 WLAN architecture standards specify that the SSID should be attached to the packet headers when sent over a WLAN. This confirms data is sent to and from the right network.
How do you find your SSID?
Most routers will have the name of the SSID labeled somewhere on the router, typically located either on the bottom, back or side. Wi-Fi network passwords, or WPA keys, should also be labeled here.
SSIDs can also be found on devices as well.
- On Windows devices, left-click on the Wi-Fi icon on the desktop taskbar to find the SSID. From there, a list of local networks labeled by their SSIDs will appear.
- On macOS, select the Wi-Fi icon on the menu bar, which then shows the available local SSIDs.
- On iOS, tap settings and select Wi-Fi, which will show a list of local networks labeled by their SSIDs.
- On an Android device, tap settings, then select Wi-Fi, which will also show a list of local SSIDs.
How do you change an SSID name or password?
The exact way to change an SSID name or password may vary slightly depending on the Wi-Fi network and router.
Through a web browser, enter the router's IP address in the address bar, then log into the router using its username and password. The username and password may be printed somewhere on the router or in its manual. Select either the Wireless, Wi-Fi Settings, Wireless Security or WLAN options. From here, there should be an option to change the SSID name and password. Once the name and password are changed, save or apply the settings. The router may need to be restarted for the changes to take effect.
The SSID and password might also be changeable through an internet service provider's (ISP's) app. If an ISP provides a mobile app to manage services or pay bills, the same app may have the option to change the SSID name or password. Likewise, an ISP may also have an app to change the SSID name or password.
A user can change the SSID to whatever they want, but it should be something recognizable without having any personally identifying information in it.
How do you secure SSIDs?
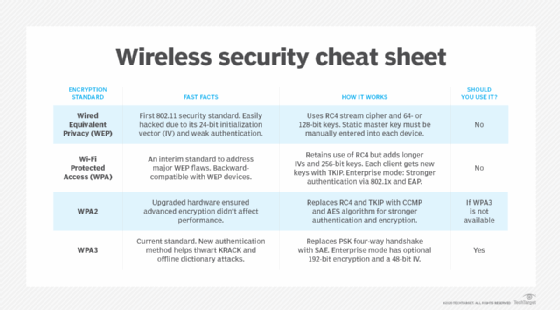
Most routers will come with a default password and encryption method, typically WPA2 or WPA3. However, there are additional wireless security methods that can be implemented, such as the following:
- Use a firewall. Routers may have a built-in firewall that can be enabled to automatically block suspicious activities on a network.
- Use a guest network. A secondary network can be set up on a router for guests only to connect to.
- Use a VPN. A virtual private network (VPN) hides the user's IP address and encrypts internet traffic, meaning others can't monitor the user's activity.
- Keep the router's firmware up to date. Security-based firmware updates help protect users from newer types of vulnerabilities or attacks.
- Change the router login credentials. Default usernames and passwords may be the same across router models, so they should be updated.
How do you hide an SSID?
SSIDs can also be hidden by turning off the SSID broadcast. This makes the SSID publicly invisible. On a surface level, hiding an SSID may seem like a good security measure, but it is not a completely safe option.
While it may seem like a good measure at first, the user's network traffic can still be tracked using freely available tools. And even though the SSID may be hidden, the IP address will stay visible.
Likewise, if a hacker finds a hidden network, they might see it as a potential target with sensitive information potentially hidden with it.