802.11n
What is 802.11n?
802.11n is an IEEE standard for wireless networking that boosts the speed, dependability and range of wireless transmissions in wireless local area networks (WLANs).
Wireless standards change every few years, and each new version is meant to bring improvements, such as higher throughput, better internet speed, increased channel bandwidth and more reliable connections.
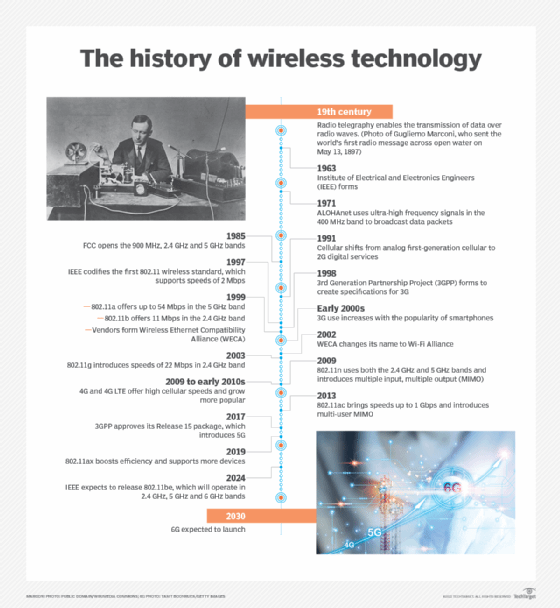
Published in October 2009, 802.11n is an update to IEEE 802.11g, which supported a maximum connection speed of 54 megabits per second (Mbps). 802.11n supports multi-channel utilization and dual band support for both 2.4 gigahertz (GHz) and 5 GHz frequencies with a maximum data rate of 600 Mbps.
Key features and techniques used in 802.11n
The 802.11n standard was published to address the increasing need for throughput brought on by the proliferation of Wi-Fi-enabled devices. The following are the key features and improvements that were introduced with 802.11n:
- Uses multiple input, multiple output (MIMO) technology and a wider radio frequency channel.
- Provides increased channel width from 20 to 40 MHz.
- Employs orthogonal frequency-division multiplexing (OFDM) to increase the data rate, while maintaining the same spectrum as 802.11a.
- Provides a mechanism called frame aggregation to decrease time between transmissions. With frame aggregation, once a station requests the channel and has the authority to transmit, it can transmit a series of frames without releasing the channel and regaining authority for each frame. This also reduces communication errors and increases data transmission speed.
- Raw data throughput with 802.11n is around 600 Mbps, which is more than 10 times that of 802.11g.
- The physical layer is implemented with enhanced signal processing and modulation, adding the capacity to transmit simultaneously over four antennas.
- The media access control (MAC) sublayer in 802.11n makes better use of the available network bandwidth, which enables a 600 Mbps theoretical maximum data transfer rate.
How does 802.11n compare to prior Wi-Fi standards?
When 802.11n was first introduced, it was met with a slow uptake before gaining acceptance. 802.11n supports multi-channel utilization and operates at both 2.4 GHz and 5 GHz bands. The maximum data rate for this wireless networking standard is 600 Mbps and it provides backward compatibility with its predecessors.
To see how it compares to the four Wi-Fi standards that came before it, it's important to examine each one of them.
802.11. The 802.11 standard was developed in 1997. It enables connections to move at 54 Mbps. 802.11 is no longer used in devices as it won't function with modern technology.
802.11a. This standard, which uses the 5 GHz frequency, was developed in 1999. Since the majority of wireless devices operate in the 2.4 GHz band, 802.11a was developed to lessen signal interferences. It provides faster speeds, with a highest data rate of 54 Mbps. However, the range is sometimes inadequate since the 5 GHz frequency has greater trouble with objects in the signal's path.
802.11b. Also created in 1999, 802.11b has a maximum speed of 11 Mbps and operates on the more common 2.4 GHz range. This was the first widely adopted Wi-Fi standard.
802.11g. Developed in 2003, 802.11g increased the top data throughput to 54 Mbps while continuing to use the dependable 2.4 GHz frequency. This led to the standard being widely adopted.
802.11n vs. 802.11ac: What are the differences?
802.11n was the fastest Wi-Fi standard for five years, before the 802.11ac or Wi-Fi 5 standards were authorized in 2014. The current Wi-Fi 6 standard, also known as 802.11ax, which was released in 2019, has since replaced 802.11ac as the most recent standard. However, Wi-Fi 7 is anticipated to succeed 802.11ax in 2024.
Despite its age, 802.11n is still the most popular Wi-Fi standard in use today due to the numerous low-end devices using it. Also, many low-cost smart home gadgets, such as wireless cameras and lightbulbs, still only use 2.4 GHz. To that end, 802.11n is a great option, as it supports both the 2.4 GHz spectrum and the optional 5 MHz band.
The following are benefits and drawbacks of 802.11n and its successor, the 802.11ac standard:
- Dual-band support. While 802.11n runs in the 2.4 GHz and 5 GHz frequency bands, 802.11ac operates only in the 5 MHz band and can support up to eight concurrent data streams.
- Connection. 802.11n works well if there are just a few devices connecting to a router. However, 802.11ac provides a better range if multiple Wi-Fi-enabled devices, such as smartphones and tablets, connect to the Wi-Fi network.
- Backward compatibility. This could be a problem with 802.11ac because it only supports 2.4 GHz, whereas 802.11n provides backward compatibility for both 2.4 and 5 GHz frequency bands.
- Speed and range. While 802.11n has a maximum data rate of 600 Mbps, 802.11ac has a range of 433 Mbps to several gigabits per second (Gbps), which is comparable to wired connections in terms of speed and performance. The 802.11ac standard boosts wireless speed by introducing a feature called beamforming and using more spatial streams that are three times broader than 802.11n.
- Cost. 802.11n might have a higher initial cost of installation. Wi-Fi 6 also involves a high cost of installation. Also, the devices that support Wi-Fi 6 are typically more expensive.
The 802.11ax, also known as Wi-Fi6, is the latest Wi-Fi standard. Learn how it differs from its predecessor 802.11ac and the various upgrades it brings.







