next-generation firewall (NGFW)
What is a next-generation firewall (NGFW)?
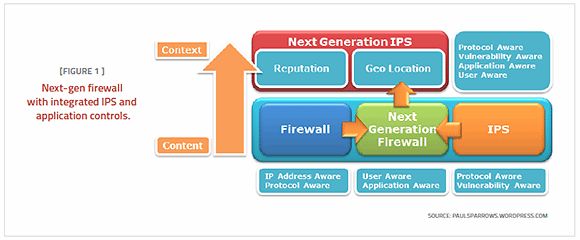
A next-generation firewall (NGFW) is part of the third generation of firewall technology that can be implemented in hardware or software. It is capable of detecting and blocking sophisticated attacks by enforcing security policies at the application, port and protocol levels.
NGFWs typically feature advanced functions including:
- application awareness;
- integrated intrusion prevention systems (IPSes);
- identity awareness -- user and group control;
- bridged and routed modes; and
- the ability to use external intelligence sources.
Of these offerings, most next-generation firewalls integrate at least three basic functions: enterprise firewall capabilities, an IPS and application control.
Like the introduction of stateful inspection in traditional firewalls, NGFWs bring additional context to the firewall's decision-making process. They provide it with the ability to understand the details of web application traffic passing through it and to take action to block traffic that might exploit vulnerabilities.
Next-generation firewall features
NGFWs combine many of the capabilities of traditional firewalls -- including packet filtering, network address translation (NAT) and port address translation (PAT), URL blocking, and virtual private networks (VPNs) -- with quality of service (QoS) functionality and other features not found in traditional firewalls. These include intrusion prevention, SSL and SSH inspection, deep-packet inspection, and reputation-based malware detection, as well as application awareness.
These application-specific capabilities are meant to thwart the growing number of application attacks taking place at Layers 4-7 of the OSI network stack.
Benefits of next-generation firewalls
The different features of next-generation firewalls combine to create unique benefits for users. NGFWs are often able to block malware before it enters a network, something that not possible previously.
NGFWs are also better equipped to address advanced persistent threats (APTs) because they can be integrated with threat intelligence services. NGFWs also can offer a low-cost option for companies trying to improve basic device security through the use of application awareness, inspection services, protection systems and awareness tools.
Next-generation firewall vs. traditional firewall
While both NGFW and traditional firewalls aim to protect an organization's network and data assets, they also have several differences.
The main similarities include static packet filtering to block packets at the point of interface to network traffic. They also both have the capability to provide stateful packet inspection, network and port address translations, and both can set up VPN connections.
One of the most important differences between traditional and next-generation firewalls is that NGFWs offer deep-packet inspection that goes beyond simple port and protocol inspection by inspecting the data carried in network packets. Other key differences are that NGFWs add application-level inspection, intrusion prevention and the ability to act on data provided by threat intelligence services.
NGFWs extend the traditional firewall functionality of NAT, PAT and VPN support to operate both in routed mode -- in which the firewall behaves as a router -- and in transparent mode -- in which the firewall behaves like a bump in the wire when it scans packets -- while also integrating new threat management technologies.