network analytics
What is network analytics?
Network analytics is the application of big data principles and tools to the data used to manage and secure data networks.
Network analytics provides deeper insight into how the network is performing and how an organization is using the network. IT can use analytics to improve security, fine-tune performance, troubleshoot subtle problems, predict traffic trends, spot potential trouble, and perform deep forensic investigations and audits.
Network analytics is most useful to organizations with complex networks, overtaxed networks or high-level security requirements. As a result, large enterprises are more likely than smaller companies to use network analytics broadly. As the tools become easier to use, more standardized, less expensive or embedded in more managed services, companies with smaller networks will find it more approachable to use analytics. But companies of every size consume network analytics as a built-in feature of cloud-managed network services, such as a network-as-a-service offering, managed software-defined WAN or managed wireless LAN service.
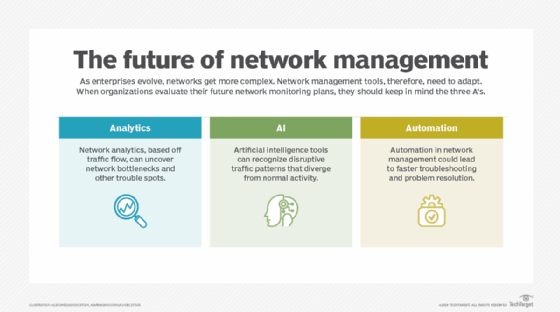
One major factor driving the growing use of network analytics is the orders-of-magnitude increase in the number of entities on the network. The continuing rise of IoT and the spread of software as code and microservices in clouds and data centers cause the number and variety of entities on the network to explode. Analytics is critical to provide comprehensive management and security in environments that grow more complex.
Analytics is also crucial to building a zero-trust environment. Zero-trust architectures require a way to close the loop between both policy and observed network behavior. Analytics that look for bad network behavior and anomalies closes that loop.
Requirements for network analytics
To take advantage of network analytics, enterprises need infrastructure capable of producing performance and usage data for the network, both low-level and high-level. That data includes the following:
- bit rates through a particular physical network port;
- collision and packet drop rates at a port;
- latencies for traffic through a port;
- number of packets or flows affected by specific security policies; and
- number of packets or flows originating from or to any given entity, be it location, device, application or identity.
Enterprises also need centralized systems to collect, store and analyze this enormous amount of information.
To be useful, network analytics needs all the user-facing accoutrements of other big data initiatives: ad hoc querying and reporting, dashboards, flexible and interactive visualization tools for exploring relationships, trends over time and anomalous events. Such tools must either be embedded in or able to integrate with key network management systems -- e.g., able to send events to a network operations center console or a zero-trust policy engine.
Network analytics for predictive analysis
Predictive network analytics is of particular interest to both network and security operations. By harnessing AI techniques, mainly machine learning, network analytics tools steadily improve at predicting future issues based on current environmental data. These newer techniques enable tools to ingest and correlate more data of more types from more sources. This, in turn, powers major improvements in the tools' ability to understand the normal behaviors of network entities -- whether hardware, software or human -- and to extrapolate likely changes in that baseline. They supplement historical trending with projections of future trending.
These newer techniques can also power better detection of anomalous behavior, potentially indicating misconfiguration, current or incipient malfunction in a system, or current or incipient attacks. Such tools can provide predictions of likely future issues. They can interpret the gradual degradation of performance in a device, such as an upcoming failure in a network card.







