SecOps and cybersecurity basics for NetOps teams
To bridge the gap between NetOps and SecOps teams, network pros should know security fundamentals, including different types of attackers, attacks and available security services.
Although both networking and security are critical to one another and to business operations, network operations and security operations teams -- NetOps and SecOps, respectively -- are commonly siloed.
Without a complete understanding of what SecOps teams do, NetOps teams may be unable to effectively help against major cybersecurity threats, such as breaches and malware. NetOps teams must understand cybersecurity basics and what a day in the life of SecOps teams looks like to enhance organizations' network security and cybersecurity strategies, said Senior Solutions Engineer Matt Allen of Viavi Solutions Inc., a network performance monitoring vendor based in San Jose, Calif.
In a webinar, Allen aimed to bridge the gap between NetOps and SecOps professionals. He explored crucial cybersecurity basics for network engineers, including different types of cyber attacks -- and attackers -- as well as the different defense layers that security services offer.
3 cybersecurity basics for network engineers
SecOps teams within organizations handle myriad cybersecurity responsibilities daily, and they constantly fight the clock to remediate issues in a timely manner. Here are three essential cybersecurity basics NetOps teams should know.
Types of cyber attackers
While some sources tout several different types of cyber attackers, they all fall under the following three umbrellas, according to Allen:
- Low-risk attackers. These attackers typically have less advanced skill sets and less patience than more advanced attackers and use freely available tools found online, Allen said. Their attacks are usually the quickest and simplest of the attacker types.
- Medium-risk attackers. These attackers have more patience than low-risk attackers. Hacktivists fall under this category, and they aim to steal intellectual property or attempt an attack due to a moral, political or general disagreement.
- High-risk attackers. High-risk attackers are willing to slowly learn employee habits and business operations over the course of months to years. These can be nation-state or organized crime attackers, Allen said, and they look to get the biggest payouts possible.
NetOps teams should know the basic indicators of cyber attackers because network data -- such as packet or traffic data -- can help track the actions of bad actors. This knowledge can enable teams to stop attacks as they happen, prevent attacks or help teams learn from mistakes if they are unable to stop an attack.
"If enterprises are worried about really skilled people that are going to take their time [with attacks], you need detailed data to hunt them down because they're going to try and be quiet," Allen said. "Network data helps with most detection and post-breach remediation."
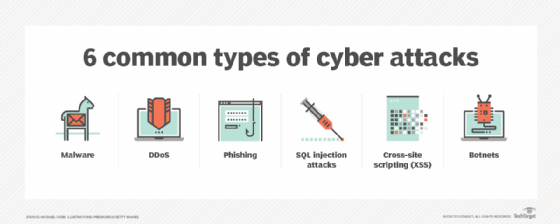
Types of cyber attacks
Like the varied types of cyber attackers, organizations can fall prey to several types of cyber attacks. The most common attacks, according to Allen, include the following:
- Advanced persistent threats (APTs). High-risk attackers are the most likely APT culprits. These attacks involve an intruder who -- undetected -- spends a long time learning about an organization, which is typically high-level, such as a governmental or financial organization. APTs typically steal data and information rather than cause major harm to networks.
- Common Vulnerabilities and Exposures (CVE). While not necessarily an attack, CVE is another category of cyber threats. Vulnerabilities and exposures provide attackers access to network resources directly and indirectly, respectively. CVE threats require patches, which SecOps teams handle for all vulnerable hardware or software.
- Phishing. Phishing attacks are most common in unsolicited emails employees receive that may appear to be from reputable sources, yet they include malicious links or attachments to steal employee credentials. Phishing is responsible for the first intrusion in 90% of data breaches, Allen said.
- Ransomware. Ransomware is an increasingly common, basic type of malware. Ransomware involves an attacker who locks or encrypts someone's data and demands payment in return. Low-risk attackers typically perform ransomware attacks, as they are a quick and easy way to get money if an organization will pay.
- SQL injections. SQL injections target classified data in order to expose it. To complete SQL injections, attackers use SQL code to gain access to encrypted resources or to change classified or sensitive data. These attacks can harm any web application with a SQL database.
NetOps teams can provide network data in APT situations if they hunt down attackers' data to see what they accessed, changed or targeted. Also, NetOps teams are arguably the most familiar with how networks operate, so they can use that expert insight to detect problems as they arise or before they cause irreparable damage.
"You've got to know your own traffic really well," Allen said. "If I know the printer should be talking to this machine, when something abnormal happens, I could hear about it. And that's going to be different for everybody, so fingerprinting and baselining [are] super important."
Types of security services
A critical factor of cybersecurity basics is the security service or services in which organizations invest. Most security services fall under one of three layers of defense, Allen said, although many services combine layers, or an organization may choose a multivendor, multilayered approach. These defense layers are the following:
- Protection. The protection layer is the moat around the castle, according to Allen. Protection services solely aim to keep unauthorized users out of the network. Examples include firewalls, VPNs and intrusion prevention systems.
- Detection. The detection layer is the castle guard: If the service perceives a threat, it alerts the SecOps team and says it should investigate the potential threat. These services don't perform any action beyond alerts. One example is an intrusion detection system.
- Respond. The respond layer comprises the knights -- or even wizards -- that take action to protect the kingdom, or network, Allen said. These services offer machine re-imaging capabilities and can actively shut down potential harmful activities on the network to verify whether something is an issue. One example is network performance monitoring and diagnostics tools.
While organizations may struggle to choose between vendors, IT teams can ask a few questions to determine which service provides which layer of defense and whether the organization needs that capability.
"Everything is evolving," Allen said. "All we really need to know is: Is this going to block traffic? Is it going to allow it and just alert on it? Or is this a tool to help you hunt down when people get inside?"
As NetOps teams spend more time on security issues, these cybersecurity basics are essential to ensure that organizations stay safe, as well as to help NetOps and SecOps teams bridge their siloed gap and work together to maintain that safety.








