What is Border Gateway Protocol (BGP)?
BGP (Border Gateway Protocol) is the protocol that enables the internet's global routing system. It manages how packets get routed from network to network by exchanging routing and reachability information among edge routers.
BGP enables peering to send packets between autonomous systems (ASes), networks managed by a single enterprise or service provider. Together, these ASes make up the public internet.
BGP creates network stability by guaranteeing that routers can adapt to route failures. When one path goes down, BGP quickly finds a new path. BGP makes routing decisions based on paths defined by rules or network policies set by network administrators.
Attributes of BGP
BGP has the following characteristics:
- Interautonomous configuration. Two ASes can connect, communicate or share information.
- Coordinated speakers. BGP speakers advertise data routes, sending peers information about the best route. They can survey each option before deciding where data goes next, requiring coordination between multiple speakers simultaneously.
- The next-hop paradigm. This paradigm decides that a data packet goes to the best choice among the potential routers available. Connections can be optimized for faster network performance, sparing administrators from doing the optimization themselves.
- Advertisement system. This system contains the path information for subsequent destinations and their accessibility.
- TCP compatibility. BGP inherits all the delivery verification features of Transmission Control Protocol (TCP) and the capacity to interface with Secure Sockets Layer, Transport Layer Security and virtual private networks.
- CIDR support. BGP supports Classless Inter-Domain Routing (CIDR), which allocates IP addresses for routing without worrying about Internet Protocol (IP) assignment or management.
How does BGP work?
Each router maintains a routing table that controls how packets are directed. The BGP process on the router generates routing table information, which is based on the following factors:
- Incoming information from other routers.
- Information in the BGP routing information base (RIB), a data table stored on a server on the BGP router.
The RIB contains information from both directly connected external peers and internal peers. It includes policies for what routes should be used and what information should be published, and it continually updates the routing table as changes occur.
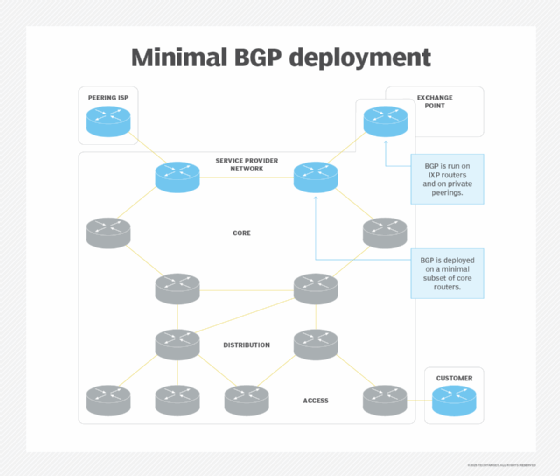
Routers located at an internet exchange point -- a physical location where different network providers exchange traffic -- are referred to as IXP routers; private peerings, on the other hand, are direct connections between specific networks, usually within the same IXP. Private peerings are not advertised broadly, enabling more regulated exchange.
What is BGP used for?
BGP helps provide redundancy by enabling routers to quickly adapt and send packets through another connection if one internet path goes down. It is often used in large networks, such as internet service provider (ISP) networks, wide area networks (WANs) and infrastructure-as-a-service (IaaS) environments.
BGP is an exterior gateway protocol, which means it is designed to share routing information between different ASes. Alternatively, an interior gateway protocol sends information within a single AS. However, Internal BGP (iBGP) can send reachability information within an organization's network.
Each BGP router maintains a standard routing table to direct packets in transit. BGP uses a client-server topology to communicate routing information, with the client initiating a BGP session by sending a request to the server.
BGP routing basics
BGP sends updated router table information only when something changes, and it sends only the affected information. BGP has no automatic discovery mechanism, which means network admins must manually set up connections between peers, with peer addresses programmed in at both ends.
BGP makes best-path decisions based on attributes, including the following:
- Highest weight.
- Current reachability.
- Hop counts.
- Local preference.
- Oldest path.
In situations where multiple paths are available -- as within a major hosting facility -- BGP policies communicate an organization's preferences for what path traffic should follow in and out. BGP community tags can control route advertisement behavior among peers.
BGP in networking is based on the TCP/IP model. It operates on the Open Systems Interconnection transport layer, or Layer 4, to control the network layer, or Layer 3.
As described in Request for Comments 4271, which was ratified in 2006, the current version of BGP4 supports both IPv6 and CIDR, which enables the continued viability of IPv4. Using CIDR enables a network to have more network addresses than with the current IP address assignment scheme.
Common BGP issues
Common issues with BGP include the following:
- Information exchange failures. Information exchanges do not always succeed, as information can be improperly formatted or contain incorrect data.
- Route flapping. Routes rapidly advertised and withdrawn can lead to packet loss and network instability.
- Convergence delays. Slow convergence, in which a network takes a long time to achieve a stable routing state after a change, can negatively affect network performance.
- Route filtering issues. Improperly configured route filters can result in route blockage.
- Router memory issues. Routers can also run out of memory or storage or be too slow to respond to updates. Routers send error codes and subcodes to communicate problems, including timeouts, malformed requests and processing problems.
Recent BGP outages
BGP outages can be vast, affecting hundreds of thousands or even millions of users. The following are some of the most notorious incidents:
- In 2023, a massive disruption of global Microsoft services occurred when a faulty security patch from CrowdStrike affected BGP routing and network connectivity across Microsoft's infrastructure, impacting many businesses and individuals using those services.
- In July 2024, Cloudflare experienced an outage that affected many websites and services dependent on its DNS resolution, resulting in disruptions and traffic anomalies.
- In March 2024, the Russian mobile operator MTS leaked tens of thousands of BGP routes from a Hong Kong internet exchange, misdirecting traffic worldwide.
- Perhaps the most notorious incident in recent years occurred on Oct. 4, 2021, when Facebook, Instagram and WhatsApp went offline for six hours. The outage was reportedly caused by the lack of working BGP routes into the social media sites and the domain name servers going offline, disconnecting the social media apps from the internet.
BGP security
BGP is also vulnerable to attacks based on misinformation. For example, malicious actors can flood a router with bad packets in a denial-of-service attack. They can also claim to be the source of routing information for an AS and temporarily control where traffic from that AS goes, a practice known as BGP hijacking.
Difference between internal and external BGP, OSPF
BGP that's used to route within a single AS is iBGP. When BGP connects one AS to others, it's called External BGP, or eBGP.
The Open Shortest Path First (OSPF) protocol is used only in internal networks. It focuses on finding the shortest route between nodes and failing over to that shortest route as quickly as possible.
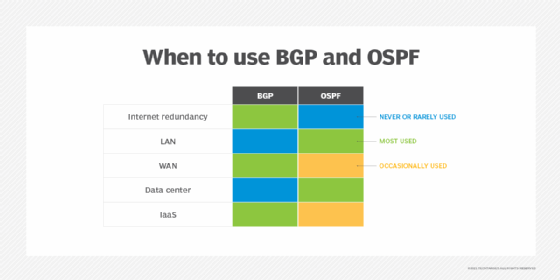
BGP is slower to fail to a new route but more scalable than OSPF. As such, OSPF is better suited for corporate local area networks (LANs) and private data centers. OSPF is essentially hierarchical in structure, while BGP is a mesh. Some networks are replacing OSPF with iBGP because of its scalability and flexibility.
Learn which network performance optimization strategies can help safeguard reliability and ensure minimal network disruptions.







