transport layer
What is the transport layer?
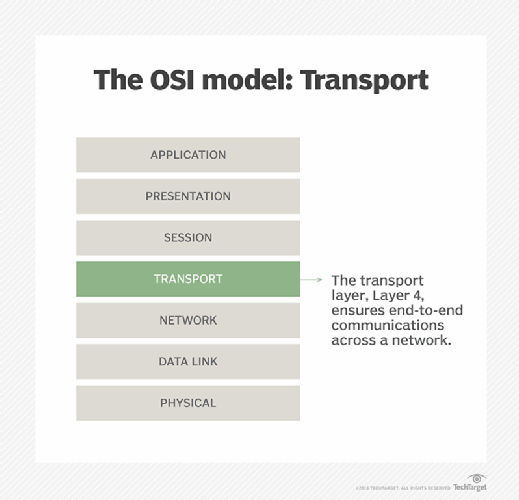
The transport layer is Layer 4 of the Open Systems Interconnection (OSI) communications model. It is responsible for ensuring that the data packets arrive accurately and reliably between sender and receiver. The transport layer most often uses TCP or User Datagram Protocol (UDP). In the TCP/IP network model, the transport layer comes between the application and network layers.
In the OSI model, the transport layer sits between the network layer and the session layer. The network layer is responsible for taking the data packets and sending them to the correct computer. The transport layer then takes the received packets, checks them for errors and sorts them. Then, it sends them to the session layer of the correct program running on the computer. The session layer now takes the well-formatted packets and uses them for the application's data.
To illustrate the transport layer, imagine a computer is a big company with many departments. The data packets are letters. The network layer is like the Postal Service that gets the letters to the correct address of the company. The transport layer is like the company mailroom. It receives the letters and does an initial inspection.
Any letters that were damaged in transit or delivered to the wrong address it reports to the sender. It then sorts the letters by department, puts them into the time order of oldest to newest and then delivers them inside the company to the correct department. The department, or application in this case, then takes the letters to read them and can build an understanding of the back-and-forth correspondence and do whatever work is needed from the letter.
Transport layer functions
The overall functionality is to insulate the application layer from needing to worry about the nitty-gritty details. It does this by providing end-to-end communication, reliability, flow control, addressing and multiplexing:
- End-to-end communication is the ability of the transport layer to provide the application a way to send and receive a stream of data. The network layer segments the data stream into packets that are sent over the network and reconstructs the data on the other end. If the data packets arrive out of order, it can reorder them by segment numbering and present the data in the correct order.
- Reliability is the ability to correct errors that can happen during data transmission over the network. If data were to be accidentally changed in transit, error correcting and checksums would catch it. If a packet were to be lost, it would be caught and retransmitted. If a single packet were to be duplicated, it could be detected and dropped. It can also send an acknowledgement of received packets for guaranteed delivery. Some protocols send a message if a packet is not received or is corrupt.
- Flow control is the ability for the transport layer to avoid sending more data than can be reliably transmitted. It can buffer sending and receiving data until there is enough network capacity for it to go through. If the receiver buffer becomes full, it can reduce the sending rate. It also implements congestion control. If a network were to become flooded with too many retransmit messages, it would be overwhelmed and not able to recover. Congestion control prevents this by using dynamic retransmission timers and slow start.
- Addressing is the ability to communicate with the correct application on the computer. Addressing typically uses network ports to assign each sending and receiving application a specific port number on the machine. By combining the IP address used in the network layer and the port on the transport layer, each application can have a unique address.
- Multiplexing is the ability for any number of applications to use any number of network connections. For example, a typical desktop computer may only have one Ethernet network connection but have several connections to the internet running at the same time, such as a web browser, video streaming and a mail client. Conversely, a large server may only have one application, such as a SQL server, but have two physical Ethernet connections to provide as much bandwidth as possible. The transport layer ensures that each application gets a fair amount of shared network connections.
Transport layer in TCP/IP model
The OSI model is a theoretical construct of how communication between systems can be understood. It does not directly relate to any specific implementation. TCP/IP, on the other hand, is a practically implemented protocol that is used in modern computer networks and on the internet.
TCP/IP may or may not implement all the features mentioned by the OSI model. Supported features depend on which protocols are used.
TCP/IP also uses less layers. In the OSI model, the transport layer comes between the network and the session layer. In TCP/IP, it comes between the network layer and the application layer.
Transport layer protocols
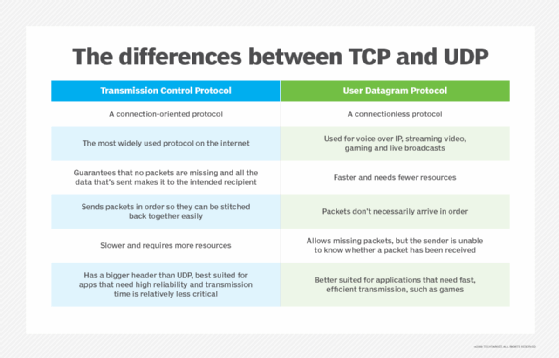
UDP and TCP are the most common transport layer protocols.
UDP is a simple and fast transport protocol. It is for connectionless transmissions. It is considered unreliable because it does not use acknowledgements or retransmissions, so packets may be lost. UDP is best for real-time data where speed of delivery is more important than reliability, such as for video conferencing.
TCP is the more feature-rich transport protocol. It is connection-oriented. It uses synchronization and acknowledgement messages to ensure delivery. It retransmits and reorders packets if needed. It can negotiate sending and receiving rates. TCP is slower than UDP. TCP is the most common protocol on the internet.
QUIC, formerly Quick UDP Internet Connections, is a new protocol. It seeks to combine many of the best reliability features of TCP with the speed of UDP. It is optimized for use over the internet and for Hypertext Transfer Protocol 3. It uses forward error correction, making it better for wireless transmissions, such as for 5G networks.
Other transport layer protocols include the following:
- Fibre Channel Protocol.
- Reliable Data Protocol.
- Stream Control Transmission Protocol.
Learn about 12 common network protocols and their functions.






