
What is FCAPS (fault, configuration, accounting, performance and security)?
FCAPS (fault, configuration, accounting, performance and security) is a network management framework and model created by the International Organization for Standardization (ISO). The primary objective of this network management model is to better understand the major functions of network management systems.
Introduced in the early 1980s, the goal was to move from a reactive form of network management to a proactive approach. This framework, for example, could empower administrators to take more control of their infrastructure in order to identify and rectify minor issues before they become major problems.
The model takes a holistic approach to managing networks, helping network professionals, like network operators, understand how network management and monitoring systems perform.
Although the FCAPS model could be considered a legacy model, it is still used in some areas, such as among communication service providers.
What does FCAPS stand for?
FCAPS is an acronym defining the five working levels, or tiers, of network management: fault, configuration, accounting, performance and security. The FCAPS model is also known as the ISO network management model or the Open Systems Interconnection (OSI) network management model. Sometimes, it is also referred to as the OSI/ISO network management model.
This article is part of
What is network management?
Fault management level
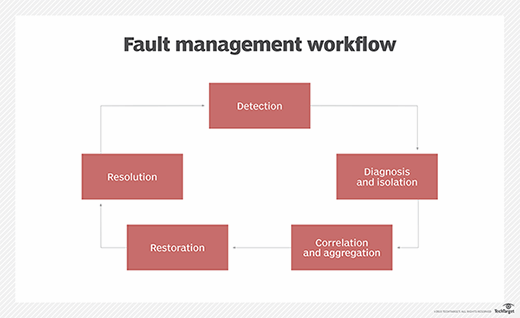
Network faults happen, so it's critical to find them early before they cause serious issues. In the FCAPS model of network management, organizations can find and correct network problems that could cause network performance failures on the fault management level.
Today, the ability to detect, isolate, log and fix potential faults is a necessary component of every network. By reviewing historical fault data, network administrators can also identify patterns and trends to enhance proactive measures that help significantly improve network stability.
They can also identify potential future issues and take steps to prevent them from occurring or recurring. With fault management, the network stays operational, while minimizing any potential downtime.
Configuration management level
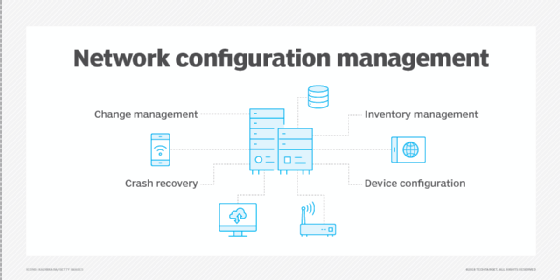
Configuration management plays a crucial role in tracking and controlling any changes made in a network. For example, it helps network administrators centrally manage deployments and related upkeep. It also tracks changes to hardware, software and network settings.
Configuration management is a critical operational capability that establishes the foundation for all other network management functions. To make this process as user-friendly and as seamless as possible, organizations must do the following:
- Centralize the storage of configurations.
- Set the stage for future expansion.
- Streamline device configurations and provisioning.
- Seamlessly track changes.
Network operation is monitored and controlled at the configuration management level. Hardware and programming changes -- including the addition of new equipment and programs, modification of existing systems, and removal of obsolete systems and programs -- are coordinated. Organizations can also keep an inventory of equipment and programs and update them regularly.
Accounting management level
The accounting management level is devoted to distributing resources optimally and fairly among network subscribers. This makes the most effective use of the systems available, minimizing the cost of operation. Sometimes called the allocation level or administration level, the accounting level is also responsible for ensuring users are billed appropriately.
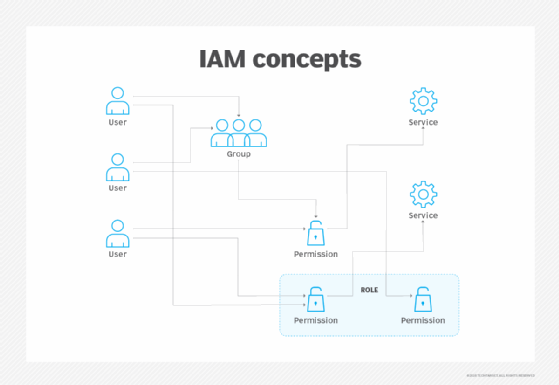
Accounting management in FCAPS helps administrators configure users and groups based on the permissions granted to them within the system. Access is also restricted to ensure that only authorized users can make significant changes to critical network systems.
Performance management level
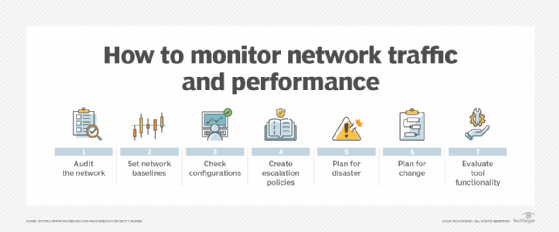
The performance management level helps better manage the network's overall performance. Organizations can maximize throughput, avoid network bottlenecks and identify potential problems. A major part of this process is determining which improvements yield the most significant overall performance enhancement.
Performance management tools enable network administrators to monitor performance and troubleshoot issues in real time, while remaining accessible and easy to use. Performance data is also regularly used to identify patterns and trends to make predictions.
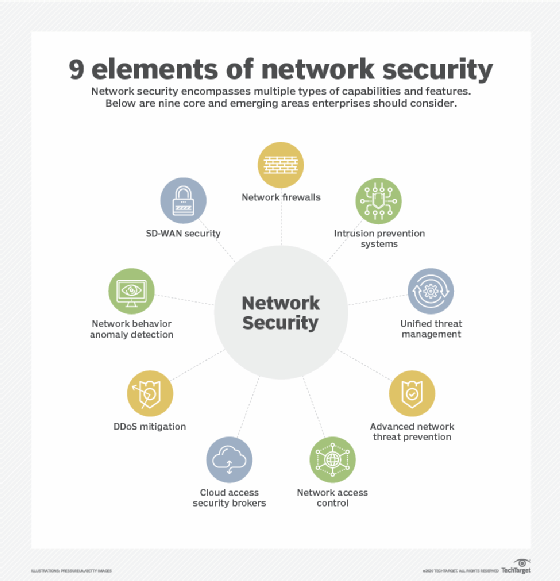
Security management level
Security management concentrates on limiting and controlling access to digital assets located within the network. This is because organizations must protect the network from hackers, unauthorized users, and physical or electronic sabotage at the security management level.
They can use encryption protocols, user authentication tools and endpoint protection to add more layers and better secure their network. Organizations can also add physical protection solutions to secure networking equipment better.
This approach helps maintain the confidentiality of user information where necessary or warranted. Security systems also enable network administrators to control what each individual authorized user can and cannot do within the system.
What does the future hold for FCAPS?
FCAPS can be considered a legacy network management model, as it isn't as widely implemented in modern network environments. This is at least partially due to newer technologies changing the network landscape enough to where FCAPS doesn't cover everything a modern network needs to be covered.
Although FCAPS is complex and far-ranging, many of its principles are outdated. For proper implementation in an IT environment, it would need to be updated and refreshed to better reflect the new realities of a modern network infrastructure.
The FCAPS security management model was conceived in a pre-cloud computing era where ownership, responsibility and control were unambiguous and straightforward. At the time, it was easy to assume that certain entities implicitly owned and controlled assets. This is not the case in every situation anymore.
When applications live in the cloud, fault detection is more challenging because teams must work with virtualized servers. For example, different tenants could experience a fault originating from the same source, like an overloaded link or an overloaded server. Upgrades can also contribute to configuration errors and faults.
As a result, organizations must secure data, applications and services that run on the cloud to ensure regulatory compliance. However, this responsibility is also shared -- to a certain extent -- by the cloud service providers who own and control the equipment.
As such, the role of FCAPS in the cloud and on-premises needs to be rethought. For example, organizations must now also define how FCAPS can help improve reliability, availability, provisioning, orchestration, cost optimization and data protection in virtualized environments.
To remain relevant, the FCAPS framework would have to adopt more modern approaches to managing networks, including those in distributed and hybrid environments.
The added use of artificial intelligence (AI) and other automation tools would also likely have to be considered when rethinking a modern FCAPS approach, as those technologies potentially enable better predictive maintenance and fault detection functions. For security, FCAPS would need to address zero trust and other modern security principles.
Those who implement the framework might also have to keep in mind how 5G networks and internet of things devices might demand more scalability.
Although FCAPS is becoming increasingly outdated, it could be updated to take into account modern and next-gen technologies. Learn more about network management with AIOps.







