
What is the network edge and how is it different from edge computing?
The network edge is where an enterprise network connects to third-party network services. Edge computing is a distributed architecture that processes data closer to end users.
Although they sound similar, an enterprise network edge is different from edge computing. So, what is the network edge exactly, and how does it compare with edge computing? This explanation of each term should help discern the differences between the two.
What is edge computing?
Edge computing is a modern take on data center and cloud computing architectures. It processes real-time applications and analysis more efficiently.
For most organizations, applications and data are housed in one or more data processing locations -- either in private data centers or public clouds. These data centers are often geographically far from the end user. This distance between the user and the apps, data and services they interact with can create inefficiencies from a bandwidth and throughput perspective.
Edge computing seeks to alleviate these inefficiencies by moving applications, data, and edge devices and servers closer to the user. This is accomplished by decentralizing traditional data centers and locating them physically closer to end users, thus placing data and apps closer to the end-user edge.
What is the network edge?
The network edge is one or more security boundaries within a network that designate who controls the underlying network infrastructure equipment. For example, an enterprise network usually consists of a corporate wired LAN, a wireless LAN, and one or more private data centers. Each of these network segments is owned and managed by the corporate IT department.
However, networks also typically include a WAN to connect remote offices, as well as connectivity to the public internet and public cloud or metro edge services. WAN connectivity usually consists of leased lines, such as MPLS or Metro Ethernet, and the internet is managed by an ISP.
The network edge is the physical point at which the enterprise-owned network connects to a third-party network. Thus, you'll often hear network administrators talk about their WAN edge, internet edge or public infrastructure edge.
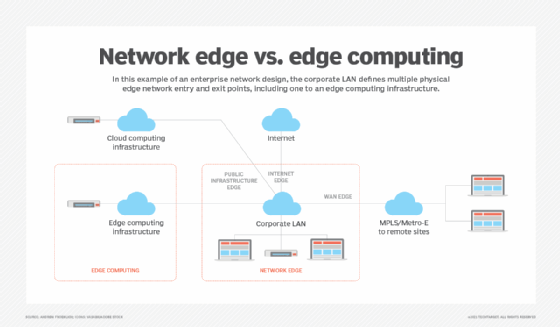
In the enterprise network design below, the corporate LAN defines multiple physical edge network entry and exit points, including one to an edge computing infrastructure.
Network edge vs. edge computing: What's the difference?
The key differences between these two terms include the following:
- Edge computing is an infrastructure separate from the corporate network that provides compute and storage services for real-time data analysis and low-latency network transport between clients and compute resources.
- The network edge is an architectural demarcation point used to identify physical locations where the corporate network connects to third-party networks.
- Edge computing infrastructures connect to corporate LANs through a network edge entry/exit point.
Network edge vs. network core: What's the difference?
Another common area of confusion is discerning the difference between the network edge and the network core. The network edge is the perimeter that separates a corporate-owned and -operated network and where it connects to third-party networks.
The network core differs from the network edge as it defines the architectural location where traffic is distributed across the corporate network using high-speed switching technologies. Traditional enterprise network designs consist of three distinct layers: network core, distribution network and access network.
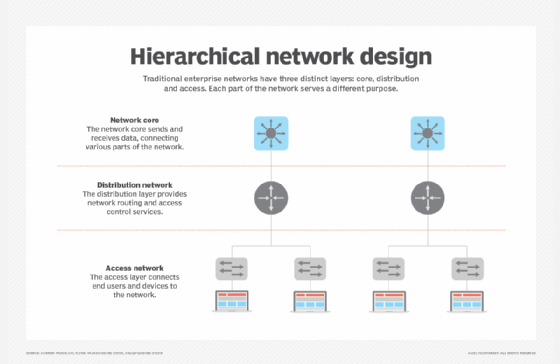
Each part of the network serves a different purpose. For example, the access network connects end users and devices to the network and provides port-based security controls. The distribution layer provides network routing and access control services that define which portions of the access layer can communicate with others on the network. Finally, the network core is designed for speed and to transmit and receive data as fast as possible, connecting the various parts of an enterprise network with great efficiency.






