
kentoh - Fotolia
What are the differences between VPN and VDI services?
With a common denominator of 'virtual,' both VPNs and VDI are common in remote work strategies. However, the technologies differ in terms of cost, use cases and performance.
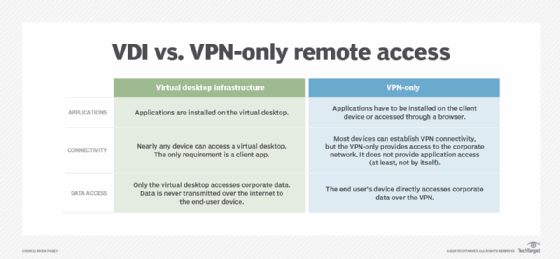
As IT teams evaluate remote access options for enterprises, VPNs and virtual desktop infrastructure, or VDI, look similar on the surface. But, when teams dig into the technical details, there are distinct differences between VPN and VDI services, as each possesses its own set of pros and cons.
Let's explore the differences between VPN and VDI technologies, what types of services they provide and a few use case deployment scenarios where each technology would work best.
What is a virtual private network?
VPNs have been around for decades. As the name suggests, a VPN's purpose is to create a secure, private network connection between two segregated networks.
One type of VPN is the remote access VPN, which creates a temporary secure tunnel between a single device and the corporate network. Employees that work from home or on the road typically use this form of VPN.
VPN software is typically installed on PCs and other smart devices. Alternatively, an OS may have built-in VPN capabilities. Once an IT team installs and configures the VPN software on a remote user's device, the user will initiate a connection and log in with single-factor or multifactor authentication. Once connected, the VPN grants the user's device access to resources on the company network.
Because VPNs have been around for so long, they are easily the most common form of remote access connectivity. However, VPN performance suffers because most users terminate their VPN into a handful of VPN gateways at the corporate network. Many businesses have migrated applications, data and services to public cloud environments, so remote access VPNs can create inefficiencies, such as bandwidth bottlenecks and hairpinning, at the corporate edge. VPN technologies also suffer from significant overhead from protocols used to build virtual tunnels and encrypt data within them.
What is virtual desktop infrastructure?
VDI was designed to stream virtual computing desktops to nearly any PC or smart device. One advantage of VDI is that, with VDI access, the user's hardware compartmentalizes everything performed within this virtual computing environment. This makes VDI much more secure from the perspective of data loss prevention.
VDIs are not used for remote access only. Instead, organizations can build VDI farms, so even employees that work directly on corporate networks can access virtual desktops for their daily jobs. Thus, the security and performance hardware requirements are far lower compared to desktop computing architectures that place OSes, applications and file storage directly on bare-metal hardware.
IT teams can also deploy VDIs with remote access gateways. These gateways enable users to connect from the internet into the virtual desktop environment.
From a performance standpoint, VDIs have more efficient bandwidth and latency and are often more cost-efficient to deploy within public cloud environments compared to similar remote access VPN gateways. However, upfront VDI costs are often much more expensive.
Making a decision: The final difference between VPN and VDI services
If an organization wants a simple way to connect remotely to the company network to access resources on the corporate LAN, stick with traditional VPN services.
However, if an organization wants to completely change how both internal and external users can securely and efficiently access both on-premises and cloud-based company resources, VDI might be a better fit.







