
Maxim_Kazmin - Fotolia
SD-WAN vs. DMVPN vs. IPsec tunnels: How do I choose?
Software-defined WAN, DMVPN and IPsec tunnels each have a place among enterprises. Our network expert compares each one and explains where they can be most beneficial.
While software-defined WAN has been the hot technology in the IT networking field for the past few years, not everyone can take advantage of it. IPsec tunnels and dynamic multipoint VPNs, or DMVPNs, still have a place in the enterprise and will continue to be viable options for years to come.
That said, IT leaders should figure out which remote connectivity options are optimal for each individual use case. Let's look at SD-WAN vs. DMVPN vs. IPsec tunnels and go over the pros and cons of each.
SD-WAN
SD-WAN is touted as a modern, cost-saving technology for connecting branch offices that require ultrareliable connectivity for low-latency and business-critical applications. SD-WAN requires two or more modes of WAN connectivity between locations. This connectivity commonly consists of MPLS and internet broadband -- or both. One goal of SD-WAN is to stretch the use of lower-cost connectivity, while meeting the same latency and throughput requirements. That's where enterprises can gain potential cost savings.
DMVPN
DMVPN can be thought of as an evolution of the standard IPsec tunnel with some added redundancy benefits. While IPsec VPN tunnels are hardcoded and essentially "nailed up" between two locations, DMVPN builds tunnels between locations as needed. It does this using typical routers with no additional feature capability, as is the case with SD-WAN.
DMVPN tunnels are designed as a mesh network, as opposed to hub and spoke. That means DMVPN can take a direct route from one remote site to another when transporting data, as opposed to being forced to route traffic through a hub location first. It can also route outbound packets around failed WAN links when they go down, if more than one WAN connection is installed at that location.
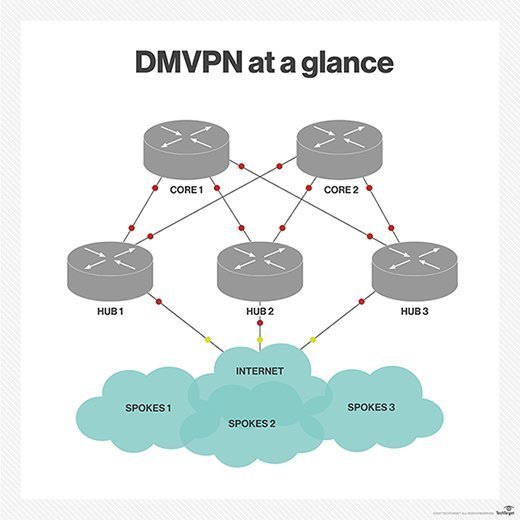
This type of WAN design is ideal when you want to build transport efficiencies between remote locations yet don't truly need the low-latency advancements found in SD-WAN. Note, however, that DMVPN uses dynamic routing protocols as its routing mechanism. Incorrect use of dynamic routing protocols can cause serious security and reliability risks when not managed properly. It also somewhat adds to the configuration complexity. As a result, it's not advisable to build DMVPN tunnels between networks you don't fully manage.
IPsec tunnels
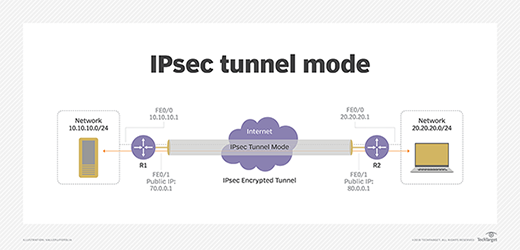
IPsec VPN tunnels used to dominate remote site connectivity. Because network managers could build tunnels across low-cost broadband internet links, IPsec tunnels were incredibly cheap compared to private WAN connectivity options, like MPLS. They're also easy to set up, and nearly everyone can acquire low-cost hardware to build an IPsec tunnel, even low-end firewalls and routers.
Choosing the right option
Technologies like DMVPN and SD-WAN are taking over remote site connectivity because they provide more efficient paths and lower latency between locations -- as long as you control both sides of the WAN. Let's briefly compare SD-WAN against DMVPN and IPsec tunnels to be sure they meet your needs without going overboard.
SD-WAN vs. DMVPN. If you have remote sites that require low-latency connectivity for the streaming of voice and video or real-time apps yet can benefit from WAN connectivity cost savings, SD-WAN might be a good fit. Keep in mind, however, that SD-WAN often requires specialized hardware, software and licensing to operate. The overall architecture can also prove to be more complex to configure and maintain. If that sounds like too much and your main concern is to be able to quickly fail over routing to a secondary connection, DMVPN may be a better fit.
SD-WAN vs. DMVPN vs. IPsec tunnels. If you need to connect your network to untrusted or temporary locations, IPsec tunnels are still the way to go. These locations include connectivity from your corporate network to third-party vendors and IaaS and PaaS cloud providers, for example. IPsec tunnels are universal, and you can build one to virtually anywhere.
The same cannot be said for DMVPN or SD-WAN. If your branch offices don't require consistent and predictable latency or the ability to fail over to a secondary WAN link, you may as well stick with traditional IPsec tunnels. There would be no business or cost savings benefit. Plus, your overall architecture and configuration setup would become unnecessarily complex for what is needed.







