
moisseyev - Fotolia
Managed vs. unmanaged switches: What are the differences?
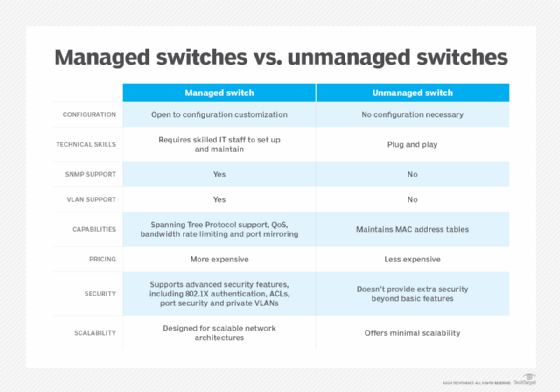
Managed and unmanaged network switches differ in various ways, including control and cost. Managed switches support more granular control, yet unmanaged switches have lower prices.
Managed switches have more capability than unmanaged switches, but they also require a skilled administrator or engineer to make the most of them. A managed switch enables better control of networks and the data frames moving through them. Unmanaged switches, on the other hand, enable connected devices to communicate with one another in their most basic form.
Below, we compare managed vs. unmanaged switches.
What are unmanaged switches?
Unmanaged switches use autonegotiated ports to determine parameters, such as data rates and whether to use half-duplex or full-duplex mode. Additionally, unmanaged switches have no concept of virtual LANs (VLANs). Thus, all devices belong to the same broadcast domain.
Unmanaged switches do maintain a media access control (MAC) address table, however. This table tracks dynamically learned MAC addresses and the corresponding switch port on which the MAC address was learned. The inclusion of a MAC address table means unmanaged network switches offer a separate, per-port collision domain.
A collision occurs when two devices within the same domain attempt to send data at the exact same time. If this occurs, the switch drops both packets, and the end devices are forced to retransmit. A collision domain is a Layer 2 network boundary where devices can send a broadcast frame and reach all devices within said segment.
What are managed switches?
Managed switches let users adjust each port on the switch to any setting, enabling them to manage, configure and monitor the network in many ways. They also provide greater control over how data travels over the network and who can access that data.
Managed switches generally offer Simple Network Management Protocol (SNMP), which enables users to monitor the statuses of the switch and individual switch ports and provides statistics like traffic throughput, network errors and port status. Network admins can track this data over time and use it for both troubleshooting and network capacity purposes.
Managed switch ports can be configured as trunks, a process that tags data frames with a VLAN ID and transports multiple VLAN frames across a single link. Trunk ports are typically used to connect two switches together or to connect a switch to a VM server that requires access to multiple VLANs. Admins can also virtually combine multiple ports to form port aggregated links that transport at two, four and eight times the speed of a single link.
Lastly, managed network switches usually have a remotely accessible console -- command-line or web interface -- to enable administrators to make configuration changes or adjustments from different physical locations.
What are the differences between managed and unmanaged switches?
The four key differences between managed vs. unmanaged switches are the following:
- control and performance
- features
- cost
- security
Control and performance. A major difference between managed and unmanaged switches is control and performance. From this standpoint, the networking team is responsible for maintaining both managed and unmanaged switches. The difference, however, is teams can configure managed switches to handle network traffic differently. Other differences include the ability to remotely access configurations and the ability to monitor devices using monitoring protocols, such as SNMP, NetFlow and other network telemetry data.
Managed switches also require one or more administrators that understand network configuration and monitoring concepts and how to apply those concepts to a switch configuration. Unmanaged switches have more of a plug and play installment process.
Features. Managed switch features may vary among manufacturers and models but often include the following:
- Spanning Tree Protocol (STP) support for switch and link redundancy without creating loops. Several STP iterations exist and are commonly configured, including traditional STP, per-VLAN STP, rapid STP and multiple STP;
- the ability to implement quality of service;
- VLAN support;
- bandwidth rate limiting; and
- port mirroring.
A unique feature of unmanaged switches is the aforementioned MAC address table. Maintaining a MAC address table helps reduce the overall number of broadcasts transmitted, limiting the number of potential collisions within the domain. This is also a key differentiator between an unmanaged switch and an Ethernet hub.
Cost. Looking at cost, unmanaged switches are considerably cheaper compared to their managed counterparts. That said, few unmanaged switch options are considered enterprise-grade. Instead, organizations interested in unmanaged switches can purchase them directly from the manufacturer online or through big-box stores.
Security. Security features can be configured on managed switches that unmanaged switches cannot use. These features include 802.1X authentication, port security and private VLANs.
What are locally managed vs. cloud-managed switches?
Locally managed switches require an administrator to be either directly connected to the corporate network or have remote access capabilities to access the switch management interface.
Cloud-managed switches, on the other hand, are controlled in public cloud environments and only require an administrator to have internet access. Thus, for geographically distributed networks, a cloud-managed switch architecture can simplify the remote management process.
How to choose between a managed and unmanaged network switch
As mentioned, managed switches are more expensive than unmanaged switches, as they require software patches, updates and -- often -- a skilled professional for implementation. That said, complex networks that consist of servers, wireless access points, PCs and IoT devices often necessitate the configuration options found on managed switches.
Small businesses with several dozen connected devices can likely get away with deploying an unmanaged switch. The capabilities found in managed switches likely won't be used, as a single flat network can easily handle the level of traffic a small network generates. Thus, a managed switch's extra cost will likely not add any additional value for the business.
An organization may require a managed switch if the business begins to approach hundreds of devices. In this case, the ability to break up the LAN into multiple broadcast domains using VLANs can ensure the network performs optimally. Additionally, larger businesses will likely have an IT network professional on staff who can configure advanced performance, security and monitoring features.





