
Denned - Fotolia
What's the difference between a router, switch and hub?
Although a router, switch and hub all help direct network traffic, the devices transmit packets in different ways. Discover the differences among these network devices.
While routers, switches and hubs are all network devices, they all serve different purposes.
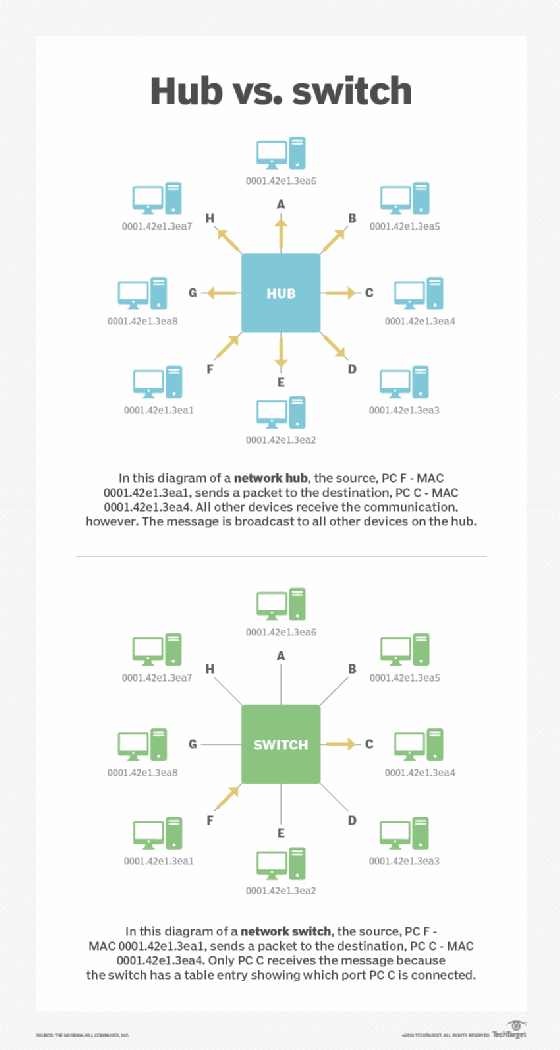
A network hub is a node that broadcasts data to every computer or Ethernet-based device connected to it. A switch is a device that channels incoming data from any one of multiple input ports to the specific output port that will take it toward its intended destination.
A router is a physical or virtual appliance that passes information between two or more packet-switched computer networks -- analyzing a given data packet's destination IP address, calculating the best way for it to reach that destination and then forwarding it accordingly.
Let's explore these devices further. First, we'll look closer at the difference between hubs and switches, and then we'll compare and contrast switches and routers.
Hubs vs. switches
The earliest Ethernet networks had no concept of virtual LANs (VLANs). Thus, an entire network consisted of a single IP subnet. If you wanted to connect two or more devices on the LAN using Ethernet, you would use a network hub.
A hub is simply a multiport Ethernet repeater that operates at the physical -- or Layer 1 -- segment of the OSI model. When the hub receives information from a sending device, it simply repeats, or broadcasts, that same information out all ports on the hub.
This video explains the differences between a
router, switch and hub.
The hub-connected device that was meant to receive the information will indeed receive it. However, so will all other connected devices. Those devices simply ignore unnecessary broadcasts. That said, a hub quickly becomes an inefficient mode of communication transport as the number of connected devices increases.
Because of this, the network switch was invented. A traditional switch operates at the data-link -- or Layer 2 -- segment of the OSI model. Switches offer two key features that differentiate them from hubs.
How a network switch works
First, a switch can segment the network into multiple, logical LANs known as VLANs. This segmentation breaks up a LAN with a single broadcast domain into multiple broadcast domains. This helps to reduce the amount of broadcast traffic congestion on larger networks.
Next, a Layer 2 switch can either statically or dynamically maintain a table that lists the switch port number along with the Media Access Control (MAC) address of the device connected to it. The beauty here is the switch no longer must repeat communications out all Ethernet ports. Instead, the switch will look in the Ethernet frames received by the sending device. The frame will contain a destination MAC address, which is cross-referenced in the switch MAC address table. If the switch knows the specific port that the MAC address corresponds to, it is sent only out that port as a Unicast frame.
In the following diagram, we see the difference between a hub and a switch:
Routers vs. switches
As mentioned earlier, Layer 2 switches can break up a single LAN into multiple VLANs. Each VLAN is its own IP subnet. Devices within the same VLAN and IP subnet can communicate at Layer 2 without any additional components. However, if a device on VLAN 10, for example, wants to communicate to a device on VLAN 20 -- this is known as interVLAN routing -- it requires a router that operates at the network, or Layer 3, segment of the OSI model.
Instead of switching frames using MAC addresses, routing between subnets uses IP addresses that are found within IP network packets that encapsulate Ethernet frames with IP address source and destination information. Traditionally, a dedicated router would provide routing services for Layer 2 switches. However, a more modern approach on enterprise networks is to use a Layer 3 switch, which combines routing and switching functions in a single device.







