
Getty Images/iStockphoto
12 common network protocols and their functions explained
Networking makes the internet work, but neither can succeed without protocols. Common network protocols and their functions are key for communication and connection across the internet.
Without network protocols, the modern internet would cease to exist.
Network protocols enable the exchange of information across the internet and work behind the scenes so effectively that many users don't think twice about them or how the internet works. But it's critical for networking professionals to know and understand protocols as the foundation of networking.
This glossary explores 12 common network protocols network engineers should be familiar with and provides information about their main functions and importance.
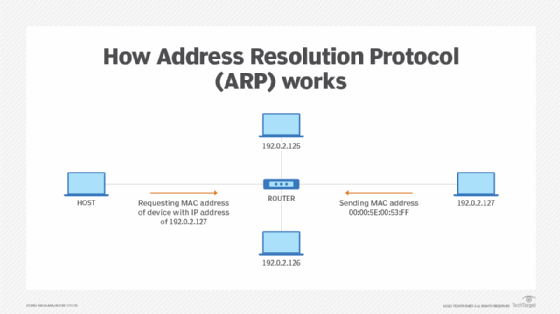
1. Address Resolution Protocol (ARP)
ARP translates IP addresses to MAC addresses and vice versa so LAN endpoints can communicate with one another. ARP is necessary because IP and MAC addresses are different lengths. Below is a breakdown of the various address lengths:
- IP version 4 (IPv4) addresses are 32 bits.
- IPv6 addresses are 128 bits.
- MAC addresses -- a device's physical hardware number -- are 12 hexadecimal digits split into six pairs.
Translations between these addresses must occur for proper device communication. ARP isn't required every time devices attempt to communicate because the LAN's host stores the translated addresses in its ARP cache. As a result, the ARP translation process is mainly used when new devices join the network.
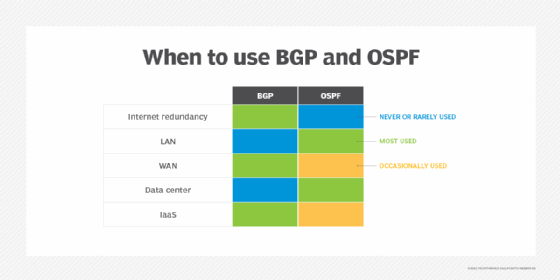
2. Border Gateway Protocol (BGP)
BGP makes the internet work. This routing protocol controls how packets pass through routers in an autonomous system (AS) -- one or multiple networks run by a single organization or provider -- and connect to different networks. BGP can connect endpoints on a LAN to one another, and it can connect endpoints in different LANs to one another over the internet.
External BGP directs network traffic from various ASes to the internet and vice versa. Internal BGP directs network traffic between endpoints within a single AS.
IoT protocols explained
Here are five of the top protocols and their features that matter most to IoT. Download your free guide now.
3. Domain name system (DNS)
DNS is a database that includes a website's domain name and its corresponding IP addresses. People use a domain name to access a website, while devices use an IP address to locate a website.
DNS translates the domain name into IP addresses, and these translations are included within the DNS. Servers can cache DNS data, which is required to access the websites. DNS also includes the DNS protocol, which is within the IP suite and details the specifications DNS uses to translate and communicate.
DNS is important because it can provide users with information quickly and enable access to remote hosts and resources across the internet.
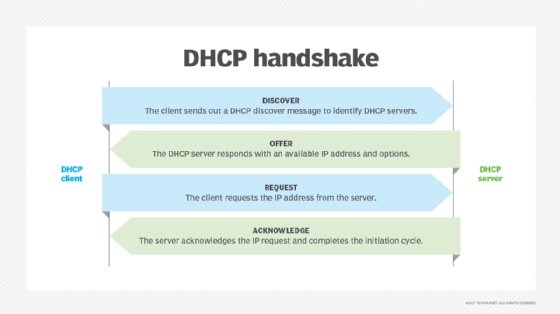
4. Dynamic Host Configuration Protocol (DHCP)
DHCP assigns IP addresses to network endpoints so they can communicate with other network endpoints over IP. Whenever a device joins a network with a DHCP server for the first time, DHCP automatically assigns it a new IP address and continues to do so each time a device moves locations on the network.
When a device connects to a network, a DHCP handshake takes place. In this handshake process, the device and DHCP server communicate using the following steps:
- The device establishes a connection.
- The server receives the connection and provides available IP addresses.
- The device requests an IP address.
- The server confirms the address to complete the process.
5. File Transfer Protocol (FTP)
FTP is a client-server protocol, with which a client requests a file and the server supplies it. FTP runs over TCP/IP -- a suite of communications protocols -- and requires a command channel and a data channel to communicate and exchange files, respectively. Clients request files through the command channel and receive access to download, edit and copy the file, among other actions, through the data channel.
FTP has grown less popular as most systems began to use HTTP for file sharing. However, FTP is a common network protocol for more private file sharing, such as in banking.
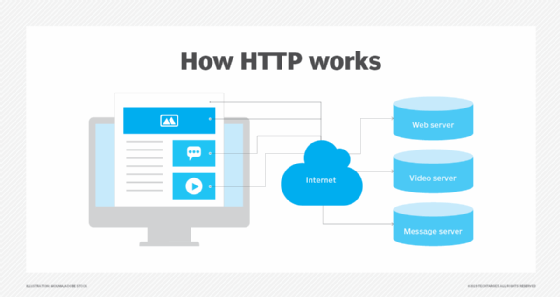
6. Hypertext Transfer Protocol (HTTP)
Like FTP, HTTP is a file sharing protocol that runs over TCP/IP. But HTTP primarily works over web browsers and is commonly recognizable for most users. When a user enters a website domain and aims to access it, HTTP provides the access. HTTP connects to the domain's server and requests the site's HTML, which is the code that structures and displays the page's design.
Another form of HTTP is HTTPS, which stands for HTTP over Secure Sockets Layer or HTTP Secure. HTTPS can encrypt a user's HTTP requests and webpages. This provides more security to users and can prevent common cybersecurity threats, such as man-in-the-middle attacks.
7. Internet Protocol (IP)
IP functions similarly to a postal service. When users send and receive data from their device, the data gets spliced into packets. Packets are like letters with two IP addresses: one for the sender and one for the recipient.
After the packet leaves the sender, it goes to a gateway, like a post office, that directs it in the proper direction. Packets continue to travel through gateways until they reach their destinations.
IP is commonly paired with TCP to form TCP/IP, the overall internet protocol suite. Together, IP sends packets to their destinations, and TCP arranges the packets in the correct order, as IP sometimes sends packets out of order to ensure the packets travel the fastest ways.
Want to learn more about common network protocols?
Check out these video definitions from TechTarget's YouTube channel, Eye on Tech, to get more insight into common network protocols.
8. Open Shortest Path First (OSPF)
OSPF works with IP to send packets to their destinations. IP aims to send packets on the quickest route possible, which OSPF is designed to accomplish. OSPF opens the shortest, or quickest, path first for packets. It also updates routing tables -- a set of rules that control where packets travel -- and alerts routers of changes to the routing table or network when a change occurs.
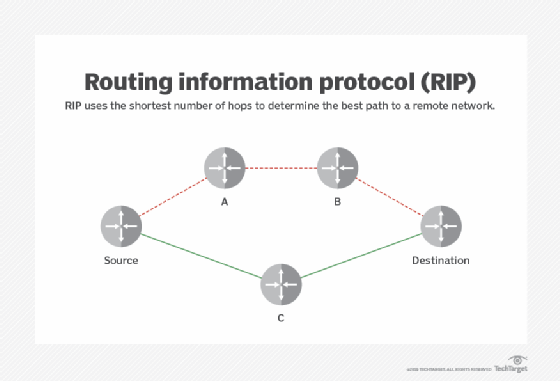
OSPF is similar to and supports Routing Information Protocol, which directs traffic based on the number of hops it must take along a route, and it has also replaced RIP in many networks. OSPF was developed as a more streamlined and scalable alternative to RIP. For example, RIP sends updated routing tables out every 30 seconds, while OSPF sends updates only when necessary and makes updates to the particular part of the table where the change occurred.
9. Simple Mail Transfer Protocol (SMTP)
SMTP is the most popular email protocol, is part of the TCP/IP suite and controls how email clients send users' email messages. Email servers use SMTP to send email messages from the client to the email server to the receiving email server. However, SMTP doesn't control how email clients receive messages -- just how clients send messages.
That said, SMTP requires other protocols to ensure email messages are sent and received properly. SMTP can work with Post Office Protocol 3 or Internet Message Access Protocol, which control how an email server receives email messages.
10. Telnet
Telnet is designed for remote connectivity, and it establishes connections between a remote endpoint and a host machine to enable a remote session. Telnet prompts the user at the remote endpoint to log on. Once the user is authenticated, Telnet gives the endpoint access to network resources and data at the host computer.
Telnet has existed since the 1960s and was arguably the first draft of the modern internet. However, Telnet lacks sophisticated security protections required for modern communications and technology, so it isn't commonly used anymore.
11. Transmission Control Protocol (TCP)
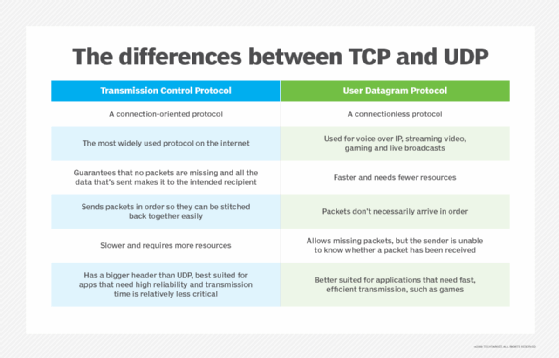
TCP is the other half of TCP/IP and arranges packets in order so IP can deliver them. Specifically, TCP numbers individual packets because IP can send packets to their destinations through different routes and get them out of order, so TCP amends this before IP delivers the packets.
TCP also detects errors in the sending process -- including if any packets are missing based on TCP's numbered system -- and requires IP to retransmit those packets before IP delivers the data to its destination. Through this process, the TCP/IP suite controls communication across the internet.
12. User Datagram Protocol (UDP)
UDP is an alternative to TCP and also works with IP to transmit time-sensitive data. UDP enables low-latency data transmissions between internet applications, making it ideal for VoIP or other audio and video requirements.
Unlike TCP, UDP doesn't wait for all packets to arrive or organize the packets. Instead, UDP transmits all packets even if some haven't arrived.
UDP solely transmits packets, while TCP transmits, organizes and ensures the packets arrive. While UDP works more quickly than TCP, it's also less reliable.
Editor's note: This article was updated to improve the reader experience.






